Apple Patents a System for Silencing Flagged Devices at the eSIM Level
Apple is building a way for mobile networks to essentially freeze out a flagged device at the hardware identity layer — not just the SIM level, but deep inside the eSIM chip itself. It's a more surgical approach to cutting off stolen or misbehaving devices than what carriers can do today.
What Apple's flagged-device eSIM lockout actually does
Imagine your phone gets stolen, or it starts behaving suspiciously on a carrier's network. Right now, carriers can block a SIM card, but a determined thief can just swap in a new one — or, on modern phones, try to download a fresh eSIM profile. Apple's patent describes a system that closes that gap.
The core idea is that when a device gets flagged — by a carrier, an equipment identity registry, or another network authority — the phone itself can be instructed to stop playing along. Specifically, the embedded chip that manages digital SIM profiles (the eUICC) gets told to freeze all profile-related activity. No new profiles can be downloaded, no switching, no workarounds.
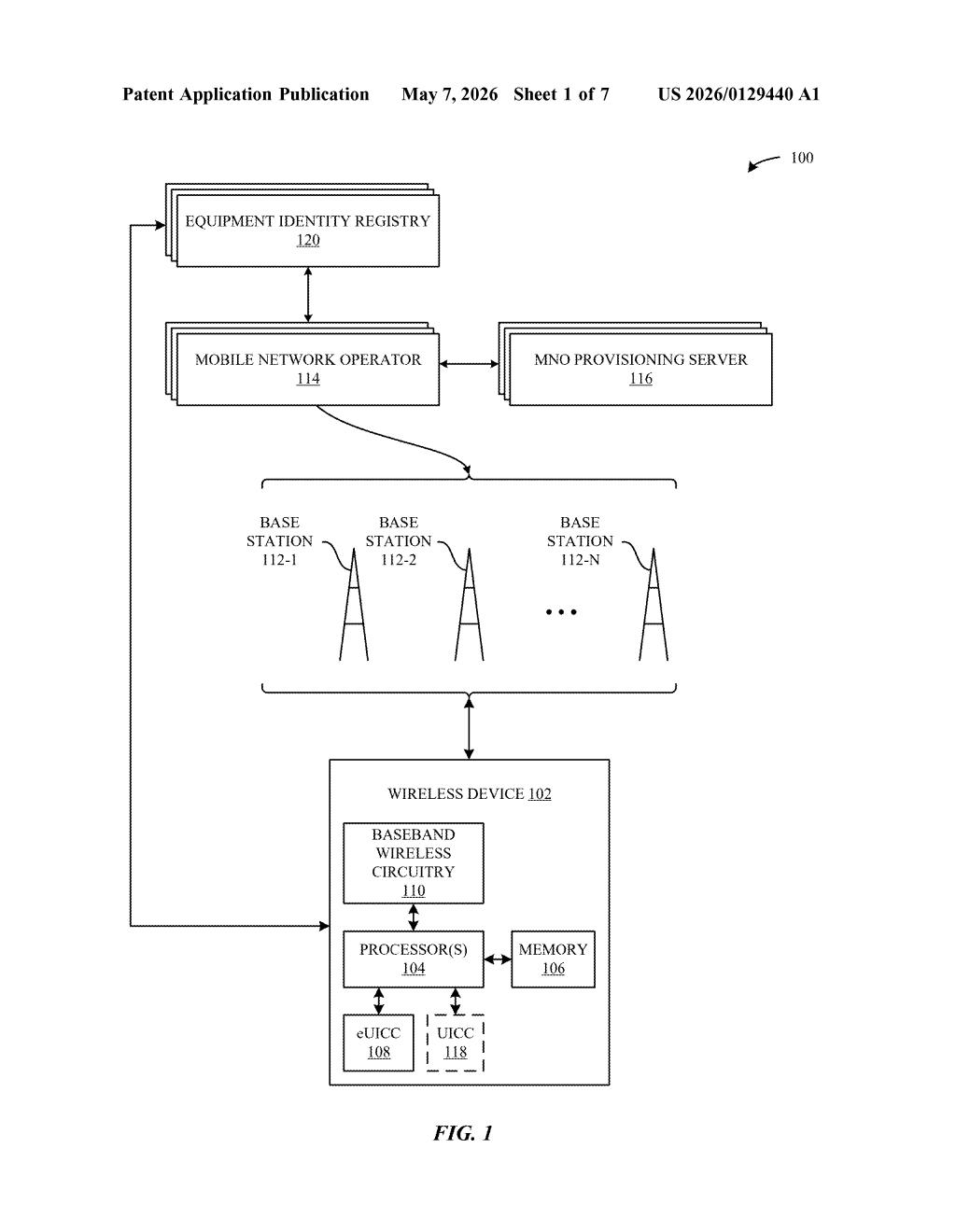
This happens through coordination between several components already inside your phone: the baseband radio chip, the eSIM's security domain, and a local profile manager. Each one has a role in detecting the failure, passing the signal, and enforcing the lockdown — without requiring the user to do anything.
How the eUICC, ISD-R, and baseband coordinate a lockout
The patent describes a three-layer lockout sequence that kicks in when a flagged device tries to attach to a mobile network and fails.
- Network attach failure notification: The baseband component (the radio chip that handles cellular communication) detects the failed connection attempt and sends a notification up to the eUICC — the embedded chip that manages eSIM profiles.
- ISD-R suspension request: The eUICC passes a request to the Issuer Security Domain Root (ISD-R) — essentially the master security gatekeeper inside the eSIM — asking it to pause all profile-related activities. Think of the ISD-R as the vault door: nothing gets in or out without its approval.
- Configuration update: The device's configuration is rewritten so that profile actions (downloading a new eSIM, switching profiles, etc.) are outright prohibited going forward.
The system is designed to work across multiple actors: Equipment Identity Registries (EIRs) that maintain blocklists of flagged device identifiers, carrier provisioning servers (SM-DP+ servers, which are the infrastructure used to push eSIM profiles over the air), and the device itself. Each can trigger or respond to the lockout depending on the scenario — stolen device, fraud detection, or policy violation.
What this means for stolen iPhones and carrier fraud
For consumers, this is mostly good news. If your phone is stolen, a more robust lockout at the eSIM level makes it significantly harder for a thief to re-activate the device on any carrier by downloading a fresh profile. Combined with existing Activation Lock mechanisms, it adds another layer that's harder to bypass because it lives in hardware-adjacent firmware.
For carriers and regulators, the patent signals that Apple is thinking seriously about eSIM fraud — an emerging attack vector as physical SIM trays disappear from flagship phones. By giving the network and the device a coordinated way to shut down profile activity cleanly, Apple could reduce the back-and-forth of unnecessary connection attempts from known-bad devices, which wastes network resources and complicates fraud investigations.
This is unglamorous but genuinely useful security infrastructure. eSIM fraud and device re-activation after theft are real problems that will only grow as eSIM becomes universal — and Apple is clearly thinking about this at the right layer. The coordination between baseband, ISD-R, and carrier servers is the kind of systems-level thinking that actually closes loopholes rather than just adding friction.
Get one Big Tech patent every Sunday
Plain English, intelligent commentary, no hype. Free.
Editorial commentary on a publicly published patent application. Not legal advice.
