Microsoft Patents a Security Engine That Blocks Files Based on Filename Tricks and Device History
Malware often hides in plain sight — a file named 'Report.pdf.exe' looks like a document but runs like a program. Microsoft's new patent describes a security engine that catches exactly this kind of trick, and uses your device's recent file history to decide whether to block it.
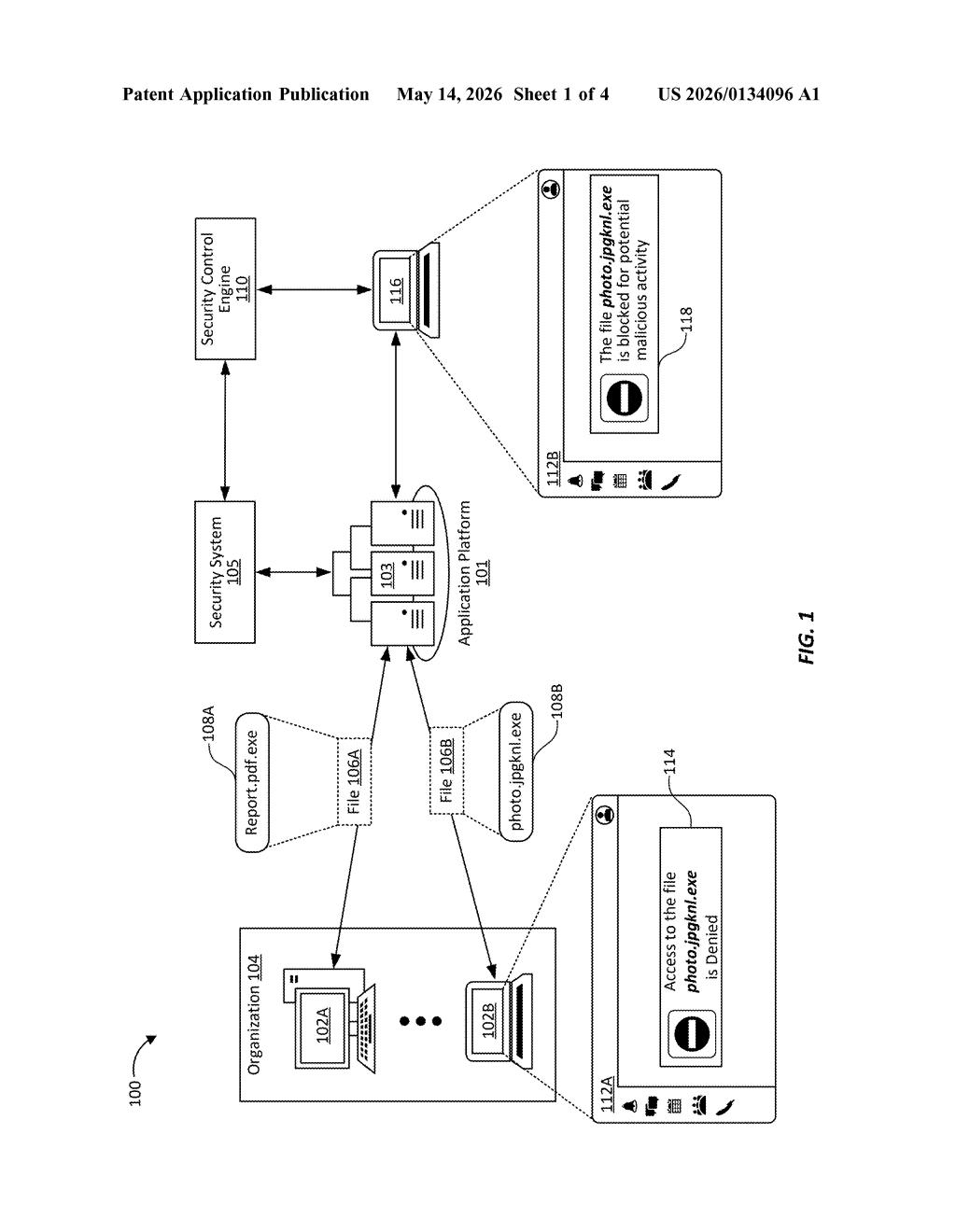
How Microsoft's filename-pattern security engine works
Imagine you download what looks like a PDF from an email, but the actual filename is Report.pdf.exe — a classic trick where attackers hide a program behind a fake document extension. Your computer might open it without question, and suddenly you have malware.
Microsoft's patent describes a security control engine that intercepts any request to open or run a file, then inspects the filename for suspicious patterns — like double extensions, misleading names, or known attacker naming conventions. If something looks off, it doesn't just block the file automatically; it also pulls up the file activity history for your specific device to get more context.
That second step is the clever part. If your device has recently been downloading a flood of weirdly named files, that's a red flag on top of a red flag. The engine combines both signals — the suspicious filename and your device's recent behavior — to decide whether to let the file run or shut it down.
How the engine parses patterns and checks activity history
The patent describes a security control engine sitting between a client device and its file system (or a networked file store). When a user or application tries to execute a file, the engine intercepts that request before anything runs.
The engine then parses the filename to extract what the patent calls a filename pattern — essentially a structural fingerprint of the name. It checks this pattern against a library of known suspicious patterns, such as:
- Double extensions (e.g.,
invoice.docx.exe) - Misleading Unicode characters that make names look legitimate
- Names that mimic trusted system files
If the filename pattern triggers a suspicion flag, the engine doesn't stop there. It retrieves the file activity history for that client device — a log of recent file operations, downloads, and execution attempts. This history provides behavioral context: a single suspicious file on an otherwise quiet machine is treated differently than the same file appearing on a device that's been churning through hundreds of oddly named files in the last hour.
Finally, the engine combines both signals — the filename pattern score and the device-level behavioral history — to make a block-or-allow decision. The claim is notably broad, covering any computing apparatus with a processor and storage that implements this two-factor file-execution gating logic.
What this means for enterprise endpoint security
This patent fits squarely into Microsoft's Defender and enterprise security product line, where endpoint protection is a core selling point. Double-extension and filename-spoofing attacks are genuinely common in phishing campaigns, and many legacy antivirus tools only catch them if a signature database has been updated. A pattern-plus-history approach means the engine can flag novel naming tricks it has never seen before, as long as they match a suspicious structural pattern.
For enterprise IT teams, the device-level history component is particularly useful — it turns individual file checks into a lightweight behavioral analysis without needing a full EDR (endpoint detection and response) pipeline. Whether this ends up as a standalone feature or folds into existing Defender for Endpoint tooling, it addresses a real and persistent attack vector.
This is solid, practical security work rather than a flashy AI play — but that's exactly why it's worth paying attention to. Filename spoofing is a perennially effective attack technique, and layering device activity history on top of pattern matching is a meaningful improvement over pure signature matching. Don't expect headlines, but do expect something like this to quietly ship in Defender for Endpoint within a year or two.
Get one Big Tech patent every Sunday
Plain English, intelligent commentary, no hype. Free.
Editorial commentary on a publicly published patent application. Not legal advice.
