Microsoft Patents a Multi-Layer Security Graph Engine for Cloud Incident Management
Managing cloud security means juggling thousands of interconnected resources — servers, identities, permissions, network paths — and querying all of that in real time is messy. Microsoft's new patent tries to make it cleaner by wrapping that complexity in a structured, multi-layer graph.
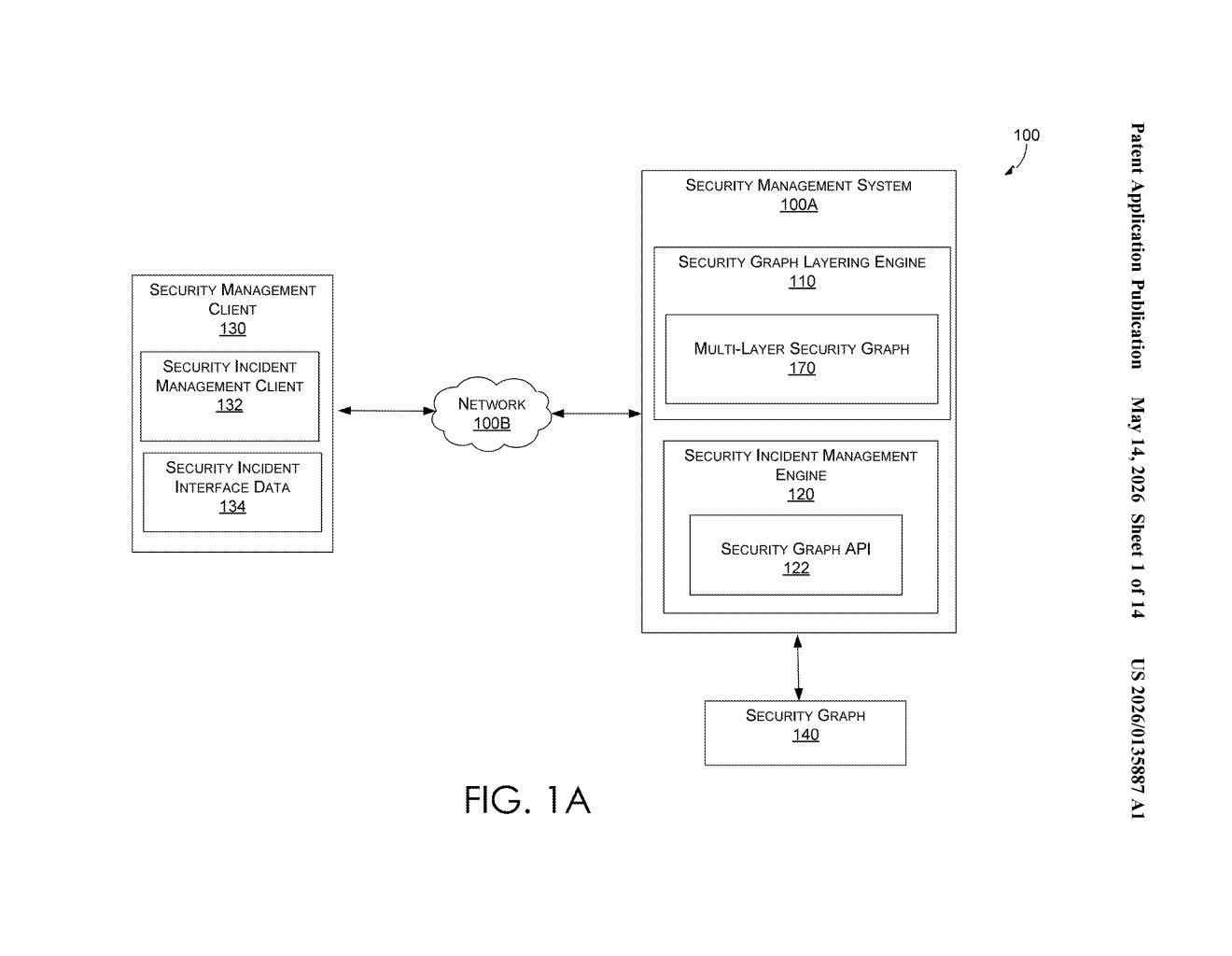
What Microsoft's security graph layering engine actually does
Imagine your company's cloud environment as a giant web of connected dots — every server, user account, database, and firewall rule is a node, and the lines between them represent relationships like 'this user can access this server.' When a security alert fires, your team needs to query that web fast to understand what's at risk. The problem is that raw security graphs are enormous and hard to search efficiently.
Microsoft's patent describes a system that takes that raw security graph and wraps it in a cleaner, structured version — called a multi-layer security graph — that's easier to query. Think of it like creating an index on top of a messy database so searches come back faster and more reliably.
The result gets sent to a security incident management dashboard, so your analysts can see query results displayed in a useful way. It's essentially a smarter middleware layer sitting between raw cloud security data and the people trying to make sense of it.
How the three-layer graph proxy handles security queries
The patent describes a security graph layering engine that sits inside a broader security management system. It ingests a raw security graph — a data structure representing relationships between cloud resources like virtual machines, identities, network policies, and storage — and transforms it into a structured proxy called a multi-layer security graph.
That multi-layer graph is divided into three distinct layers:
- Configuration layer — defines how the graph is structured and what data it contains
- Presentation layer — controls how results are formatted and displayed to end users
- Query layer — handles the actual execution of security queries against the graph
When a security analyst submits a query (like 'show me all resources accessible from this compromised identity'), the system routes that query through the multi-layer graph rather than hitting the raw underlying data directly. The query executes, generates a query result, and sends it back to the security incident management client for display.
The separation of concerns here — config, presentation, and query as distinct layers — is the architectural bet Microsoft is making. It's a pattern borrowed from software design (think MVC architecture) and applied to security graph infrastructure.
What this means for cloud security operations teams
Cloud environments at enterprise scale can have millions of security-relevant relationships to track. Security teams using platforms like Microsoft Defender for Cloud or Microsoft Sentinel already rely on graph-based data models to understand attack paths and blast radius. A layered proxy architecture could let those platforms run more complex queries without grinding to a halt — which matters a lot when you're triaging an active incident.
For security operations center (SOC) analysts, faster and more reliable graph queries mean quicker answers during the most stressful moments. It's the kind of backend plumbing improvement that doesn't make headlines but directly affects how quickly a team can contain a breach.
This is solidly useful infrastructure work, not a flashy AI play — but that's fine. The three-layer graph proxy pattern is a real engineering answer to a real problem that anyone running cloud security at scale has felt. It fits cleanly into Microsoft's existing Sentinel and Defender ecosystem, and the architecture is sensible enough that you'd expect to see something like this ship quietly in a product update within a year or two.
Get one Big Tech patent every Sunday
Plain English, intelligent commentary, no hype. Free.
Editorial commentary on a publicly published patent application. Not legal advice.
