IBM Patents a Secret Manager for Locking Down Cloud Workload Credentials
Every time a cloud app spins up, it needs passwords, API keys, and certificates — and those secrets are often the weakest link in the whole system. IBM's new patent tries to solve that by giving each cloud workload its own dedicated secret-keeper.
What IBM's cloud secret manager actually does
Imagine your company's cloud app needs a database password to start up. Right now, that password might travel through multiple systems before it reaches the app — and any one of those stops is a potential leak. IBM's patent describes a smarter handoff.
A component called a secret manager sits inside the cloud workload itself. When the host server sends a setup request, the secret manager grabs any sensitive information — passwords, tokens, API keys — and holds it in its own protected memory. The app never has to go hunting for its credentials from an outside system.
When the application actually needs that information, it asks the secret manager directly. The secret manager hands it over in a controlled, auditable way. The idea is that secrets stay inside a tight boundary rather than floating around where other processes — or attackers — might intercept them.
How the secret manager intercepts and stores credentials
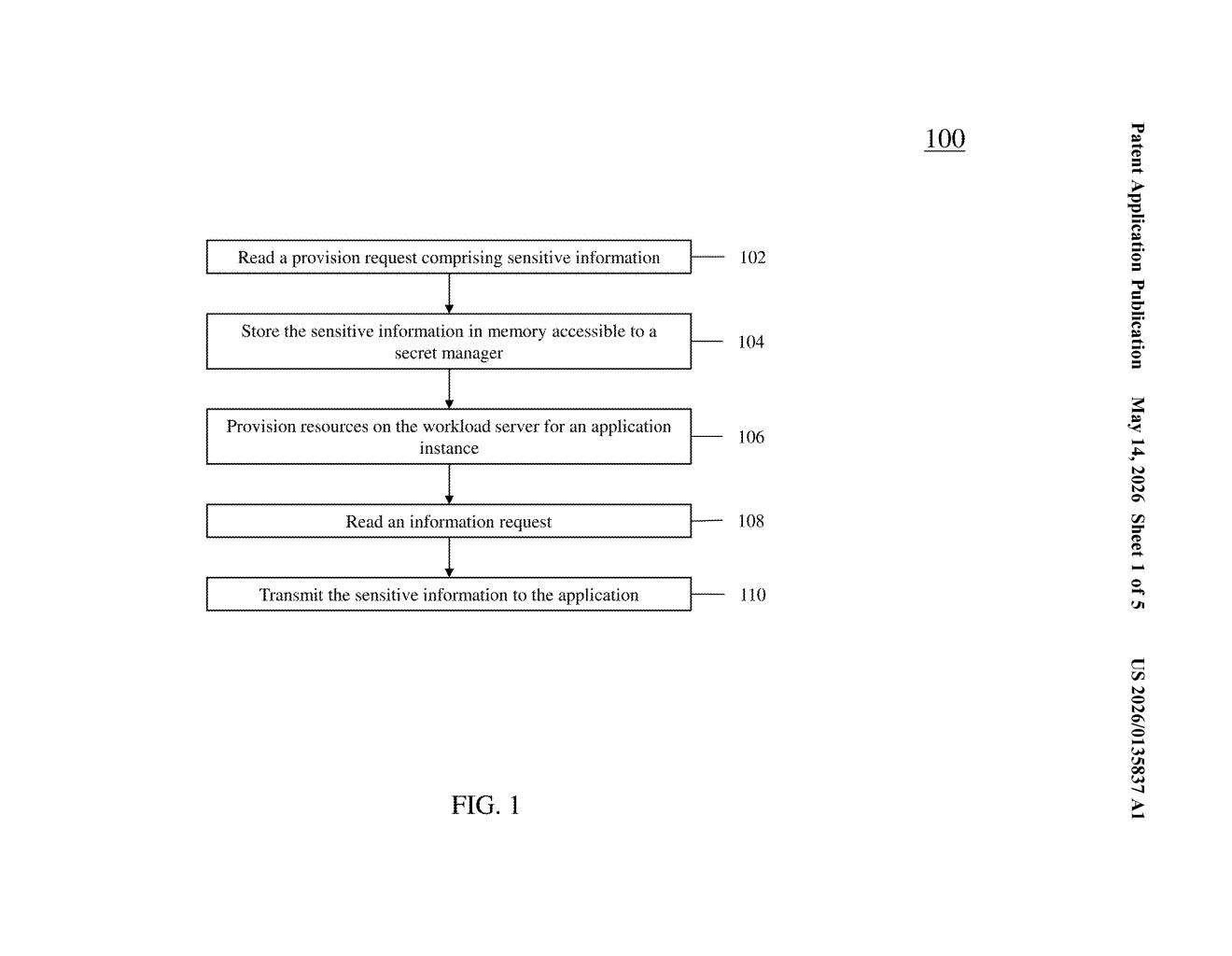
The patent describes a cloud workload architecture that centralizes credential handling through a dedicated secret manager component. Here's the basic flow:
- The host server sends a provisioning request — essentially a startup instruction — that includes sensitive information like credentials or configuration secrets.
- The secret manager reads that request and immediately pulls the sensitive data into memory that only it can access, isolating it from the broader workload environment.
- The secret manager then provisions resources on the workload server for an application instance, but without exposing the secrets to the provisioning process itself.
- When the application instance needs its credentials, it sends an information request to the secret manager, which then transmits the secrets directly to that specific instance.
The key design principle here is least-privilege isolation — the idea that sensitive data should only be readable by the exact component that needs it, for the shortest time necessary. By having a dedicated in-workload secret manager rather than relying on external secret stores alone, IBM's design tries to reduce the attack surface at the moment an app spins up, which is historically a vulnerable window.
What this means for enterprise cloud security posture
Cloud credential leaks are one of the most common causes of enterprise data breaches — and they often happen not because an attacker broke encryption, but because a secret traveled through too many hands on its way to an application. This patent addresses that problem at the workload layer, which is where IBM's enterprise customers actually run their sensitive jobs.
For IBM Cloud and its hybrid-cloud customers, a built-in secret manager at the workload level could simplify compliance with frameworks like SOC 2, HIPAA, and PCI-DSS — all of which require tight controls on how credentials are stored and transmitted. If IBM bakes this into its cloud platform tooling, it becomes a selling point for regulated industries that are already a core IBM customer base.
This is solid, unsexy infrastructure work — the kind of security plumbing that enterprise buyers actually care about when evaluating cloud platforms. It's not a breakthrough concept (HashiCorp Vault and AWS Secrets Manager cover similar ground), but building it natively into the workload layer rather than as an external dependency is a meaningful architectural distinction. IBM is clearly targeting regulated enterprise workloads where credential hygiene is a procurement requirement, not a nice-to-have.
Get one Big Tech patent every Sunday
Plain English, intelligent commentary, no hype. Free.
Editorial commentary on a publicly published patent application. Not legal advice.
