Microsoft Patents Low-Cost Masking Circuit for Post-Quantum Cryptography
Quantum-resistant encryption is only useful if attackers can't extract keys by watching power consumption or timing. Microsoft's new patent targets that exact vulnerability — cheaply.
What Microsoft's quantum-safe crypto masking actually does
Imagine a thief who can't crack your safe directly, so instead they watch how long it takes you to open it, or measure tiny fluctuations in the electricity your safe uses — and from that, they figure out your combination. That's called a side-channel attack, and it's a real threat to hardware that runs encryption.
The standard defense is called masking: you split your secret data into random-looking pieces so that no single piece leaks useful information. The problem is that masking is expensive — it adds circuits, power consumption, and latency that chip designers hate.
Microsoft's patent describes a leaner way to do masking specifically for post-quantum cryptography (the new wave of encryption algorithms designed to resist quantum computers). By shuffling how numbers are converted between two different mathematical representations — and rotating a single bit at a clever moment — the circuit achieves strong protection without the usual overhead.
How the A2B/B2A bit-shifting pipeline hides secrets
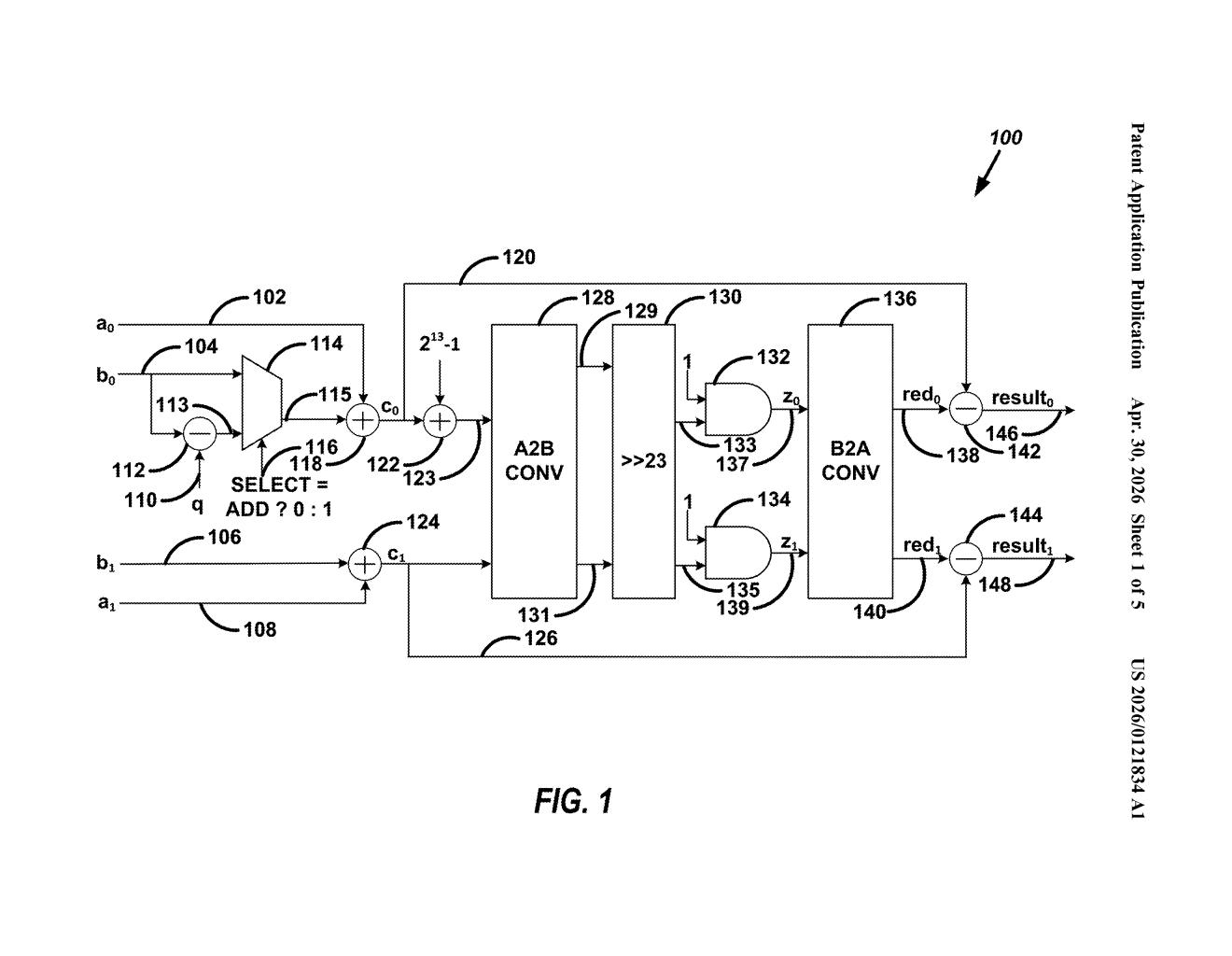
The patent describes a modular adder and subtractor circuit — the basic arithmetic building block inside post-quantum cryptographic algorithms like CRYSTALS-Kyber or CRYSTALS-Dilithium — that includes built-in masking at low cost.
The core trick involves three stages:
- Arithmetic-to-Boolean (A2B) conversion: The circuit takes numbers represented as ordinary sums (arithmetic domain) and converts them into bitwise XOR-based representations (Boolean domain). This domain switch is where most masking schemes get expensive.
- Bit rotation (the shifter): The most significant bit (the highest-value bit, which often leaks the most information about carries and overflows) is rotated to become the least significant bit. This single-bit move is cheap in hardware — just rewiring — but it breaks the correlation an attacker would exploit.
- Boolean-to-Arithmetic (B2A) conversion: The rotated values are converted back to arithmetic representation so the rest of the cryptographic computation can proceed normally.
The result is two masked arithmetic values that represent the original sum or difference, without ever exposing the underlying secret in a form a side-channel attacker can use. The inventors claim this approach reduces the area and latency cost compared to conventional masking schemes for post-quantum algorithms.
Why cheaper side-channel protection matters for PQC hardware
Post-quantum cryptography is coming to every device you own — NIST finalized its first PQC standards in 2024, and the clock is ticking for hardware makers to implement them. The hard part isn't just making the math quantum-resistant; it's making the implementation resistant to physical attacks, especially in constrained devices like smart cards, IoT sensors, and secure enclaves.
Side-channel resistance is usually the most expensive part of that equation. If Microsoft has genuinely found a way to cut that cost — even modestly — it's meaningful for every chip designer building PQC into low-power silicon. This is the kind of unglamorous infrastructure patent that quietly ends up in firmware for billions of devices.
This is genuinely useful work, not a vanity filing. The post-quantum transition is a hardware problem as much as a math problem, and masking overhead is one of the real engineering bottlenecks. The bit-rotation trick is elegant — simple enough to be believable as a real cost-saver, novel enough to be worth patenting.
Get one Big Tech patent every Sunday
Plain English, intelligent commentary, no hype. Free.
Editorial commentary on a publicly published patent application. Not legal advice. Patentlyze may earn a commission if you click an affiliate link and make a purchase. This doesn't affect what we cover or how we cover it.
