Microsoft Patents a System That Blocks Dangerous Cloud Config Changes Before They Ship
Every major cloud breach has a root cause, and a surprising number of them start with a misconfigured deployment — a firewall rule left open, a storage bucket made public. Microsoft's new patent describes a system designed to catch exactly those mistakes before they ever touch production.
How Microsoft catches risky cloud configs before they go live
Imagine your team is about to push a configuration change to your cloud infrastructure — maybe opening a new network port or granting a service broader permissions. Right now, most teams rely on code reviews and manual checklists to catch security mistakes. But humans miss things, especially under deadline pressure.
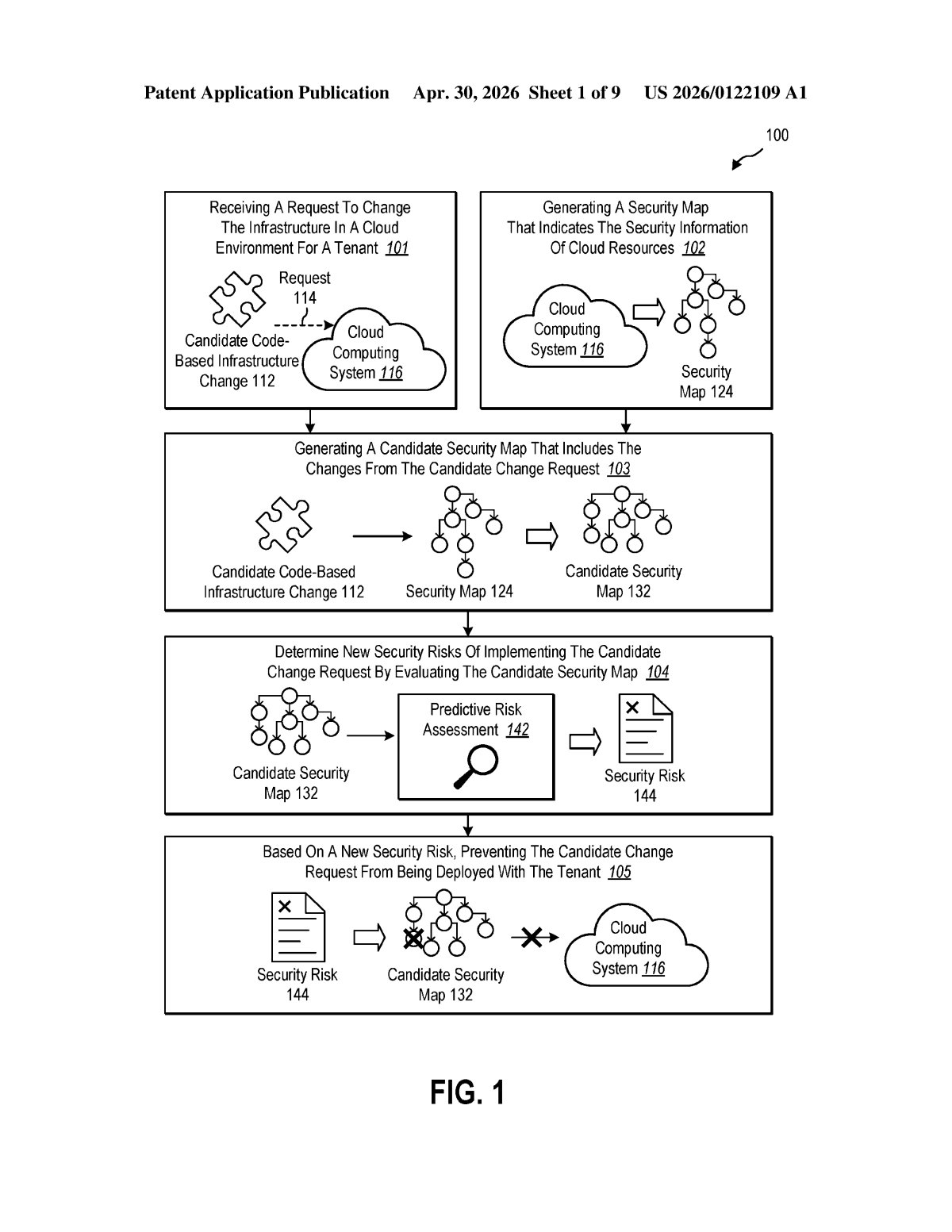
Microsoft's patent describes a system that automatically intercepts those changes before they deploy. It builds a kind of security map of your current cloud setup — think of it like a wiring diagram that also labels which connections are sensitive — then simulates what your cloud would look like after the proposed change is applied.
If that simulation reveals a new attack path or vulnerability, the system can block the change outright, flag it for review, or even automatically suggest a fix. The goal is to make dangerous misconfigurations impossible to accidentally ship — not just easier to detect after the fact.
How the security map catches risky config patterns
The system operates as a pre-deployment security gate inside a cloud computing environment. When a developer or automated pipeline submits a candidate code-based infrastructure change (think Terraform, ARM templates, or Bicep files), the system springs into action before anything is provisioned.
First, it generates a security map — a graph structure where nodes represent cloud resources (VMs, storage accounts, network interfaces) and edges represent relationships between them, annotated with security metadata like access permissions and exposure levels. This map reflects the current, live state of the environment.
Next, it creates a candidate security map by merging the proposed changes into that graph. This produces a hypothetical view of what the environment would look like post-deployment. The system then runs security pattern analysis (essentially graph-based rule matching — scanning the graph for known dangerous configurations, like a public-facing resource with a path to sensitive data) against pattern-based data structures derived from the candidate map.
- If a new security risk is detected, the deployment is blocked
- If a reportable breach pattern is found, it's flagged for the security team
- Optionally, the system can automatically modify the candidate change to eliminate the vulnerability before resubmitting
Critically, the system is described as lightweight and runtime-aware — it uses live resource information, not just static policy files, which means it can reason about the actual security posture of a tenant at the moment of deployment.
What this means for cloud DevOps and infrastructure security
Cloud misconfigurations are consistently one of the top causes of data breaches — not because engineers are careless, but because modern cloud environments are extraordinarily complex. A change to one resource can inadvertently open a path through five others. Shifting security checks into the deployment pipeline itself, rather than relying on post-deployment scanning, is a meaningful architectural improvement.
For Microsoft, this fits squarely into its Azure security story and its broader push around tools like Defender for Cloud and the Microsoft Security Copilot platform. If this system ships in some form, it could make Azure infrastructure deployments meaningfully safer by default — the kind of thing that shows up in enterprise procurement checklists and compliance conversations.
This is a genuinely useful idea, and the graph-based 'simulate-then-analyze' approach is smarter than simple policy rule matching. The automatic remediation angle is the most interesting part — if it works reliably in practice, it turns a blocking gate into a helpful collaborator rather than just another deployment friction point. The hard part, as always, will be keeping false positives low enough that teams don't just route around it.
Get one Big Tech patent every Sunday
Plain English, intelligent commentary, no hype. Free.
Editorial commentary on a publicly published patent application. Not legal advice. Patentlyze may earn a commission if you click an affiliate link and make a purchase. This doesn't affect what we cover or how we cover it.
