IBM Patents an AI System That Flags IT Config Policy Gaps Automatically
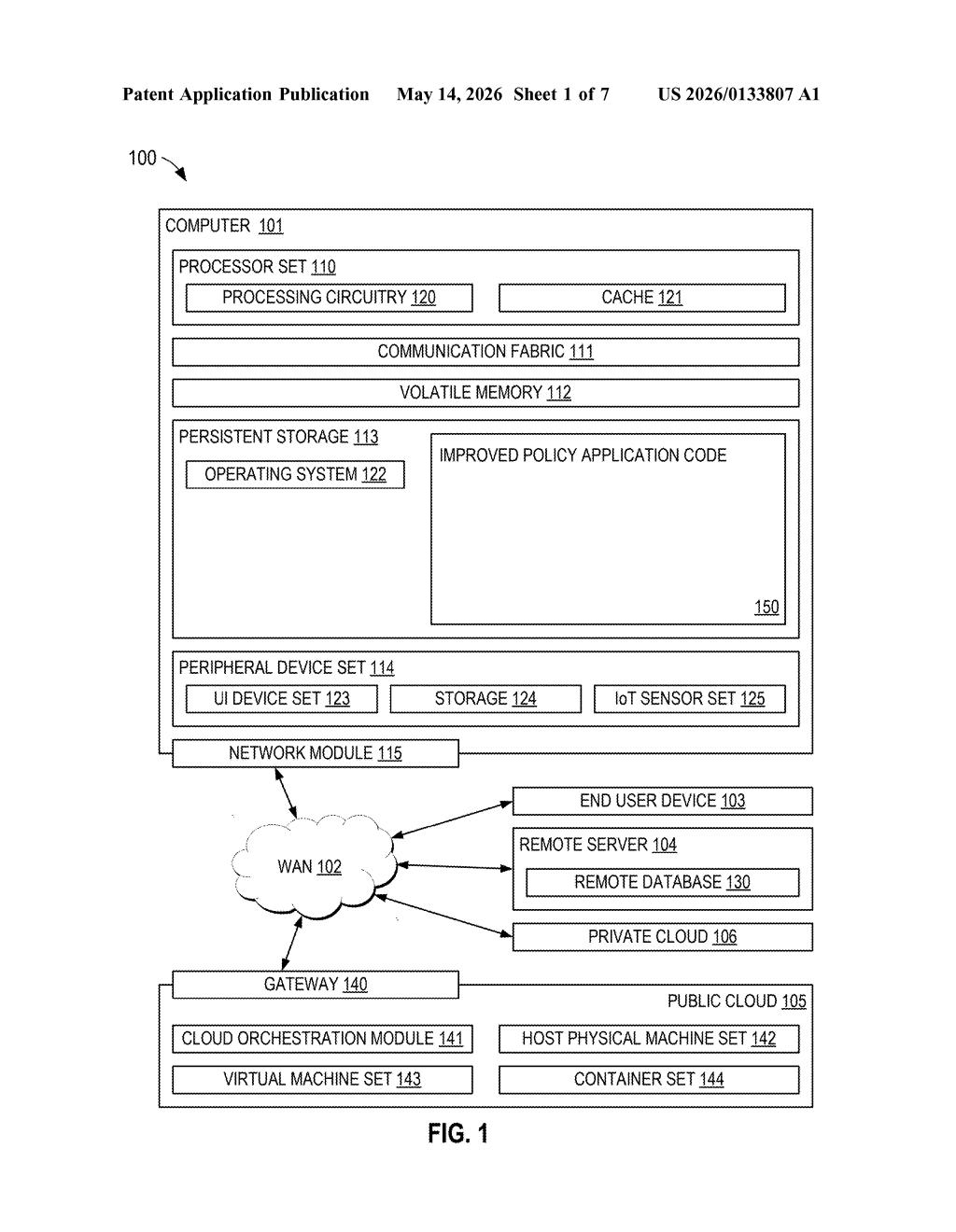
Manually auditing whether a sprawling cloud environment actually follows your security policies is tedious, error-prone work. IBM's new patent describes an AI system that reads your infrastructure configs, compares them against policies, and surfaces the most problematic gaps — automatically.
What IBM's policy-adherence scanner actually does
Imagine your company has hundreds of servers, cloud services, and network devices, each with its own configuration file. Somewhere in those files, a setting probably violates a security or compliance policy — but finding it means reading through thousands of lines of technical config text and cross-referencing it against policy documents. That's a job that today falls on overworked IT and security teams.
IBM's patent describes a smarter approach: an AI model that ingests your configuration files, breaks them into logical chunks, and generates plain-language summaries of each chunk. It then compares those summaries against your policy documents to score how relevant each chunk is to a given policy and how well it actually follows that policy.
The end result is a prioritized report. Instead of wading through everything, you get a focused list of the configuration blocks that matter most to your policies and are most out of compliance — the highest-risk items, surfaced first.
How IBM's ML model scores configs against policies
The system works in two broad phases: preprocessing and scoring.
During preprocessing, the patent describes splitting raw configuration data — think YAML files, firewall rules, or cloud resource definitions — into discrete entities (individual settings or components) along with their metadata. A trained ML model then generates natural-language summaries of each entity, essentially translating technical config syntax into something that can be meaningfully compared against policy text.
Next comes the relevance and adherence scoring step. The system computes two separate scores for each entity against each policy:
- Relevance — does this config entity even apply to this policy?
- Adherence — if it does apply, is it actually compliant?
Entities are then clustered into configuration blocks using embedded vectors (mathematical representations of meaning that let the system group semantically related settings together, even if they're in different files or formats). Relevance and adherence scores are recomputed at the block level.
Finally, the system prepares a final report by selecting configuration blocks that score highest on relevance and lowest on adherence — in other words, the stuff that matters most and is most broken. This triage-first approach is the core practical value of the patent.
What this means for enterprise compliance teams
For large enterprises, keeping cloud and on-premise infrastructure aligned with security and regulatory policies (think SOC 2, ISO 27001, or internal baselines) is a constant, expensive struggle. Today that work is largely manual or relies on rigid rule-based scanners that only catch known violations. IBM's approach uses semantic understanding — the AI actually reads and reasons about configurations — which could catch policy violations that a keyword-matching tool would miss.
For IBM's consulting and hybrid cloud business (think IBM Security and IBM Cloud), this kind of tooling fits neatly into their enterprise IT management portfolio. If this makes it into a product like IBM Security QRadar or IBM Turbonomic, compliance teams could spend less time triaging audit findings and more time fixing the real problems.
This is solid, unglamorous enterprise infrastructure work — exactly the kind of AI application that actually gets deployed and used, even if it never makes headlines. The triage-first reporting model (highest relevance, lowest adherence) is a genuinely sensible design choice that shows IBM is thinking about the practical workflow, not just the ML pipeline. Don't expect this to ship as a flashy consumer feature, but it's the kind of incremental AI tooling that enterprise security buyers will pay for.
Get one Big Tech patent every Sunday
Plain English, intelligent commentary, no hype. Free.
Editorial commentary on a publicly published patent application. Not legal advice.
