Google Patents a Timed Rotation System for Ephemeral Cryptographic Keys
Every secure connection you make relies on cryptographic keys — and how often those keys rotate is a quiet but critical detail. Google's new patent describes a system that generates, caches, and automatically expires those keys on a strict timed schedule.
How Google's key caching rotates your secure sessions
Imagine your front door lock gets automatically rekeyed every hour. Any copy of the old key instantly stops working, and anyone who needs in must use the fresh one. That's roughly the idea behind Google's new patent.
Google's system generates a pair of cryptographic keys — one public, one private — at the start of each defined time window. These keys get stored in a fast-access memory cache and are used to establish or continue all secure communication sessions during that window. When the window closes, the keys are deleted.
The practical upside: even if someone intercepts a key, it's only useful for a short, bounded period. The system also avoids generating a brand-new key for every single connection, which would be slow and expensive at scale. It's a middle ground between security and performance — and Google clearly wants it automated.
Inside Google's ephemeral keyset generation and cache lifecycle
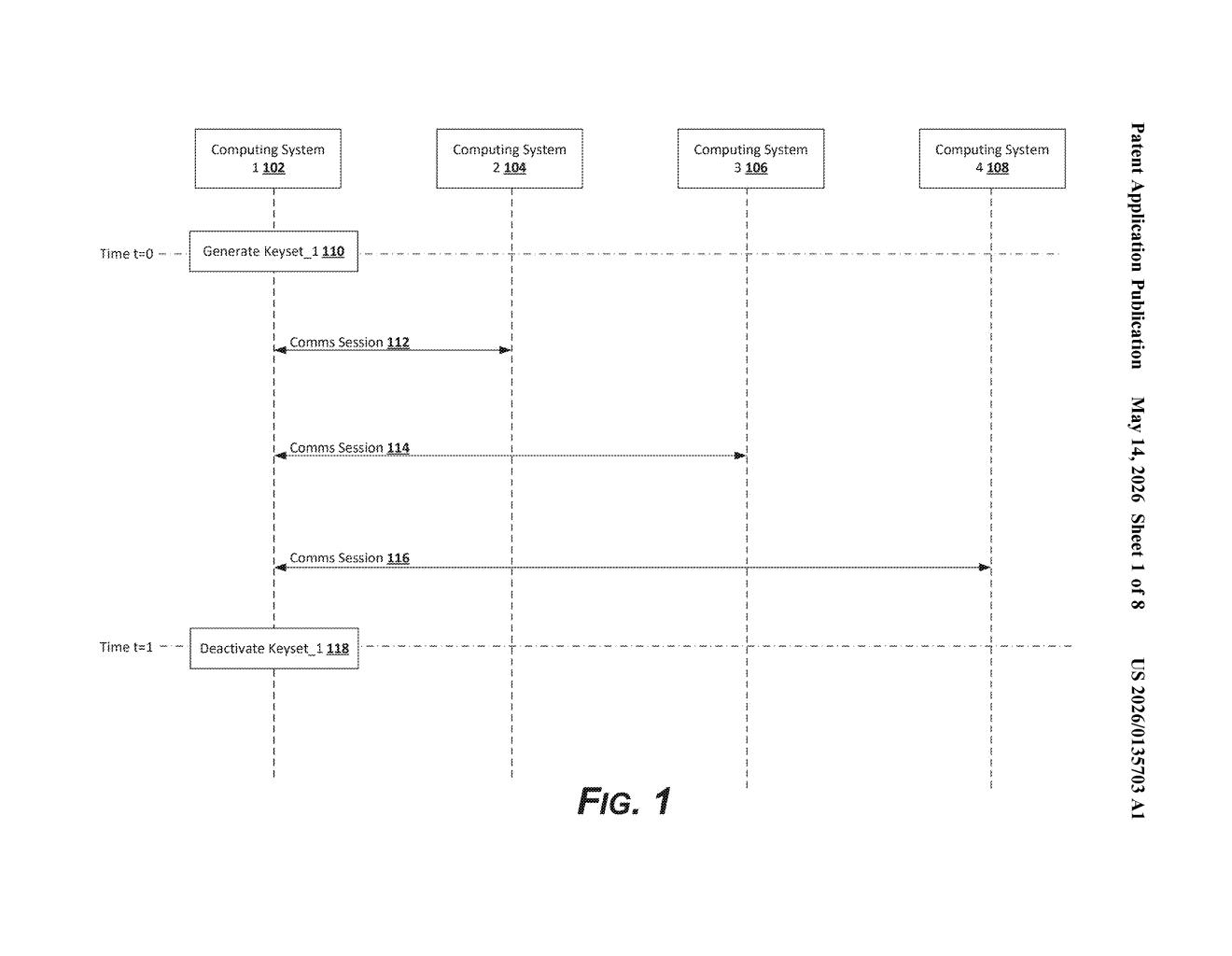
The patent describes a periodic key generation and caching mechanism for securing network communications. At the start of each key re-use period (a configurable time window), a computing system generates a fresh ephemeral keyset — a matched pair of public and private cryptographic keys that are temporary by design.
That keyset is written to a memory cache (fast, in-RAM storage rather than disk), making it quickly accessible for any connection requests that arrive during the window. Any secure session — whether new or resumed — uses this same cached keyset for authentication and encryption handshakes.
- Key generation is triggered by the start of each period, not by individual connection requests.
- Key reuse across multiple sessions reduces per-connection cryptographic overhead.
- Key deletion is automatic at period expiration — nothing lingers in cache.
The "asynchronous" framing in the title is meaningful: key generation happens on its own schedule, independent of when connections arrive. This decouples the performance-sensitive connection path from the heavier work of key generation, which matters a lot when you're handling millions of sessions simultaneously.
What rotating key caches mean for large-scale secure infrastructure
At Google's scale — Cloud, Gmail, Search, YouTube — millions of TLS and other encrypted sessions are established every second. Generating a unique key pair per session is cryptographically ideal but operationally brutal. This patent describes a practical tradeoff: share keys across sessions within a short window, rotate automatically, and delete on expiry. That's a well-understood pattern in forward secrecy design, but automating and caching it cleanly at infrastructure scale is non-trivial.
For you as an end user, this is invisible plumbing — but it's the kind of plumbing that determines whether a data breach exposes one hour of traffic or months of it. The bounded key lifetime is the real security win here.
This is solid, unsexy infrastructure work. The pattern — ephemeral keys, timed rotation, automatic expiry — is well-established in cryptographic best practices, but engineering it reliably at hyperscaler scale with low latency is genuinely hard. The fact that Google is patenting the specific caching and async generation mechanism suggests this is productionized internal tooling they want IP protection on, not a speculative research idea.
Get one Big Tech patent every Sunday
Plain English, intelligent commentary, no hype. Free.
Editorial commentary on a publicly published patent application. Not legal advice.
