IBM Patents a Faster Way to Push Security Patches Into Containers
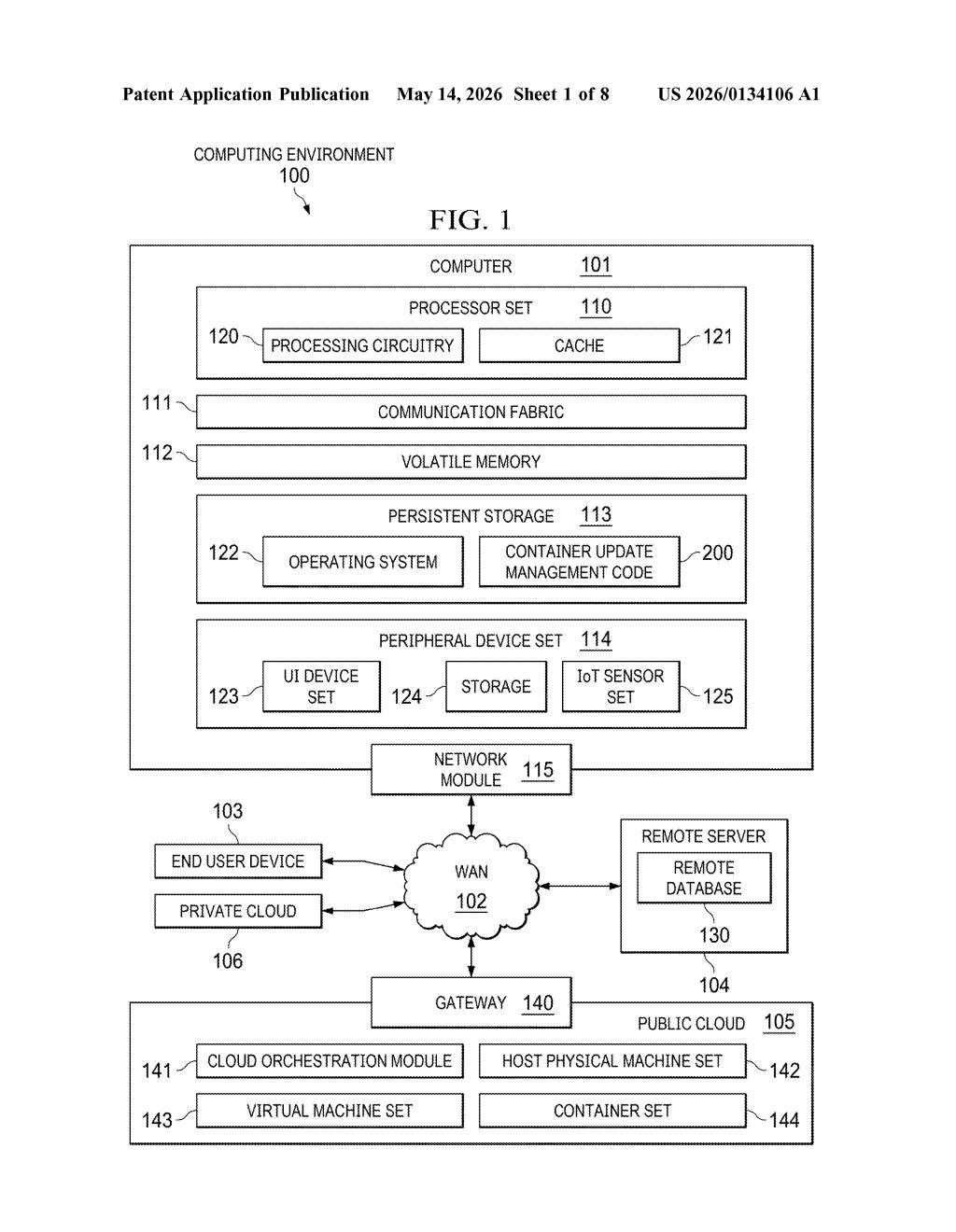
Patching containers is a constant headache for cloud teams — every fix risks breaking the immutable image underneath. IBM's new patent tries to solve that by reserving a dedicated spot at the top of the container stack just for security updates.
What IBM's reserved-layer container patching actually does
Imagine you rent a furnished apartment (a container image) and something in it needs fixing — say a leaky faucet (a software vulnerability). Normally you'd have to tear down and rebuild the whole apartment to make the repair. That's roughly how containers work today: they're designed to be immutable, so patching them is disruptive.
IBM's idea is to pre-designate a special top shelf in every container — a reserved top image layer — specifically for security patches. When a vulnerability fix comes in, the system downloads it, then slides it into that reserved spot using a tracking tag (a cache identifier). No rebuilding required.
The result: you can push security updates to running containers concurrently, without rebuilding images from scratch each time. For teams managing hundreds or thousands of containers, that's a meaningful reduction in patching complexity and downtime.
How IBM moves patches through the container layer stack
Container images are built in stacked, read-only layers — think of them like a layered cake where each slice is a filesystem snapshot. Normally, patching a vulnerability means baking a new cake from scratch, which is slow and operationally expensive.
This patent describes a two-step mechanism:
- Download step: The vulnerability fix is first pulled into a standard container layer — a temporary staging area.
- Move step: The fix is then relocated into a reserved top image layer, a dedicated patch-only zone that sits at the top of the image stack. A cache identifier (essentially a lookup key that maps the patch to its correct destination) guides the placement.
By controlling where in the layer hierarchy the patch lands, IBM's method avoids invalidating the lower layers of the image. The cache identifier is the key piece — it lets the system match an incoming patch to the right reserved slot without manual intervention.
The claim is deliberately minimal right now: download, then move. But the underlying architecture implies a management system that tracks which containers have which reserved layers and which patches have been applied — hinting at a broader orchestration layer around this core mechanic.
What this means for cloud security and DevOps pipelines
For cloud-native teams running Kubernetes clusters or large container fleets, vulnerability patching is one of the most operationally painful tasks — especially when each fix requires a full image rebuild and redeployment cycle. IBM's approach, if it works as described, could let security teams push patches across many containers simultaneously without triggering that whole pipeline.
The reserved layer concept also has implications for compliance: if patches always land in a known, auditable location, verifying that a fix was applied becomes much simpler. That's a quiet but real win for regulated industries like finance and healthcare where patch verification is a mandatory step in every audit.
This is a solid infrastructure idea solving a real, unglamorous problem — container patching is genuinely painful at scale and IBM is right to attack the layer-architecture constraint. That said, the patent claim as filed is very narrow (just download + move), so whether IBM has truly locked up the broader reserved-layer concept remains to be seen. It's worth watching if you work in cloud security tooling, but don't expect headlines.
Get one Big Tech patent every Sunday
Plain English, intelligent commentary, no hype. Free.
Editorial commentary on a publicly published patent application. Not legal advice.
