Microsoft Patents a Key Rotation System That Never Exposes Your Encrypted Data
Rotating encryption keys is a security best practice — but doing it usually means either holding onto old keys or laboriously re-encrypting everything. Microsoft's latest patent tries to make that tradeoff disappear entirely.
How Microsoft keeps encrypted data safe during key rotation
Imagine your company stores millions of files encrypted with a password. Every few months, security policy says you need to change that password. The problem: all those files were locked with the old password. You either have to keep the old password around forever (risky), or unlock and re-lock every single file with the new one (painfully slow and expensive).
Microsoft's patent describes a smarter layered approach. Instead of encrypting your files directly with the password users know, a permanent master key does the actual locking and never leaves a secure remote server. The password users rotate is just a key to that master key — not to the files themselves.
When you rotate the access password, the files don't change at all. The server just updates which password it accepts before handing out the master key. Old passwords get discarded, new ones take over, and your data stays encrypted the whole time without a single file being touched.
How the primary key and access key stay separate
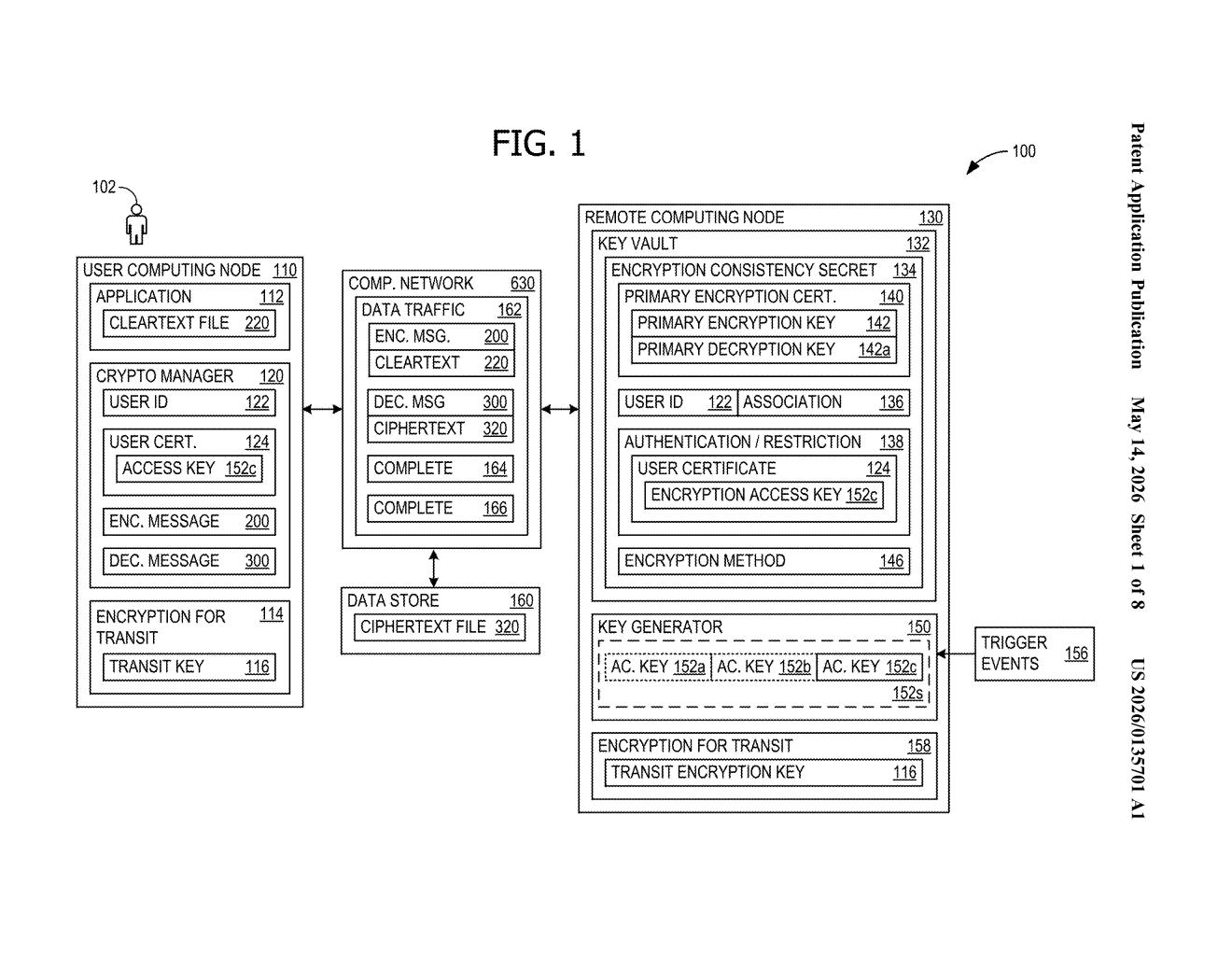
The system introduces two distinct layers of cryptographic material: a primary encryption key and an encryption access key.
The primary encryption key is generated once on a secure remote node — think of it as a key vault or hardware security module — and it never leaves that environment. All actual file encryption and decryption is performed there. Users never receive this key directly.
The encryption access key is what users and applications hold. It acts as a credential that unlocks access to the primary key. When a user wants to encrypt or decrypt a file, they send a request to the remote node along with their current access key. The node validates the access key, performs the cryptographic operation using the primary key, and returns the result — without ever exposing the primary key itself.
The clever part is key rotation: on a trigger event (a scheduled interval, a security incident, a policy change), the access key is replaced with a new one. The remote node updates its association so that only the new access key grants entry. Because the primary key never changed and the files were always encrypted with it, no re-encryption is needed. Old access keys can be safely discarded, closing the window of exposure that comes from retaining deprecated credentials.
What this means for cloud storage and compliance costs
For enterprises managing cloud storage at scale, re-encryption during key rotation is a genuine operational headache — it consumes compute, introduces downtime risk, and creates windows where data may be partially re-encrypted. This approach eliminates that cost entirely, making frequent rotation more practical and therefore more likely to actually happen.
From a compliance standpoint, regulations like HIPAA, PCI-DSS, and various government frameworks mandate regular key rotation. A system that makes rotation cheap and safe removes a real barrier to meeting those requirements. It also fits naturally into Azure Key Vault's existing architecture, which suggests Microsoft could be positioning this as infrastructure for a future managed encryption service — or hardening one that already exists.
This is a genuinely useful piece of cryptographic infrastructure engineering — not flashy, but the kind of thing that prevents real-world security incidents. The insight of separating 'the key that encrypts data' from 'the key that proves you can access that key' is clean and well-understood in security circles, but having a patent on a specific implementation in cloud-scale key vault architecture is a meaningful stake in the ground for Microsoft's enterprise security portfolio.
Get one Big Tech patent every Sunday
Plain English, intelligent commentary, no hype. Free.
Editorial commentary on a publicly published patent application. Not legal advice.
