Red Hat Patents a Cloud-to-Local Secrets Manager Topology Migrator
Migrating sensitive credentials off the cloud without scrambling how they're organized is a real operational headache — and Red Hat thinks it has a cleaner answer.
What Red Hat's secrets topology migrator actually does
Imagine your company stores hundreds of passwords, API keys, and certificates across different cloud-based vaults, each organized by geography or business unit. One day you decide to bring all of that in-house — maybe for compliance, cost, or security reasons. The nightmare scenario: you move everything, but the structure gets flattened or lost, and suddenly no one knows which secret belongs where.
Red Hat's patent is for a system that solves exactly that. It reads the existing layout of your cloud-based secret managers — which secrets live where, how they're grouped, what parameters define them — and then rebuilds that same structure inside a local secret manager. You end up with a faithful on-premises copy that mirrors your cloud setup.
Think of it like a moving company that doesn't just haul your furniture, but reassembles every room exactly as it was. The patent is a continuation of an earlier filing from 2023, meaning this idea has been in development for a while.
How the migrator maps and replicates secret topology
The patent describes a system built around three core operations: topology discovery, parameter association, and structured migration.
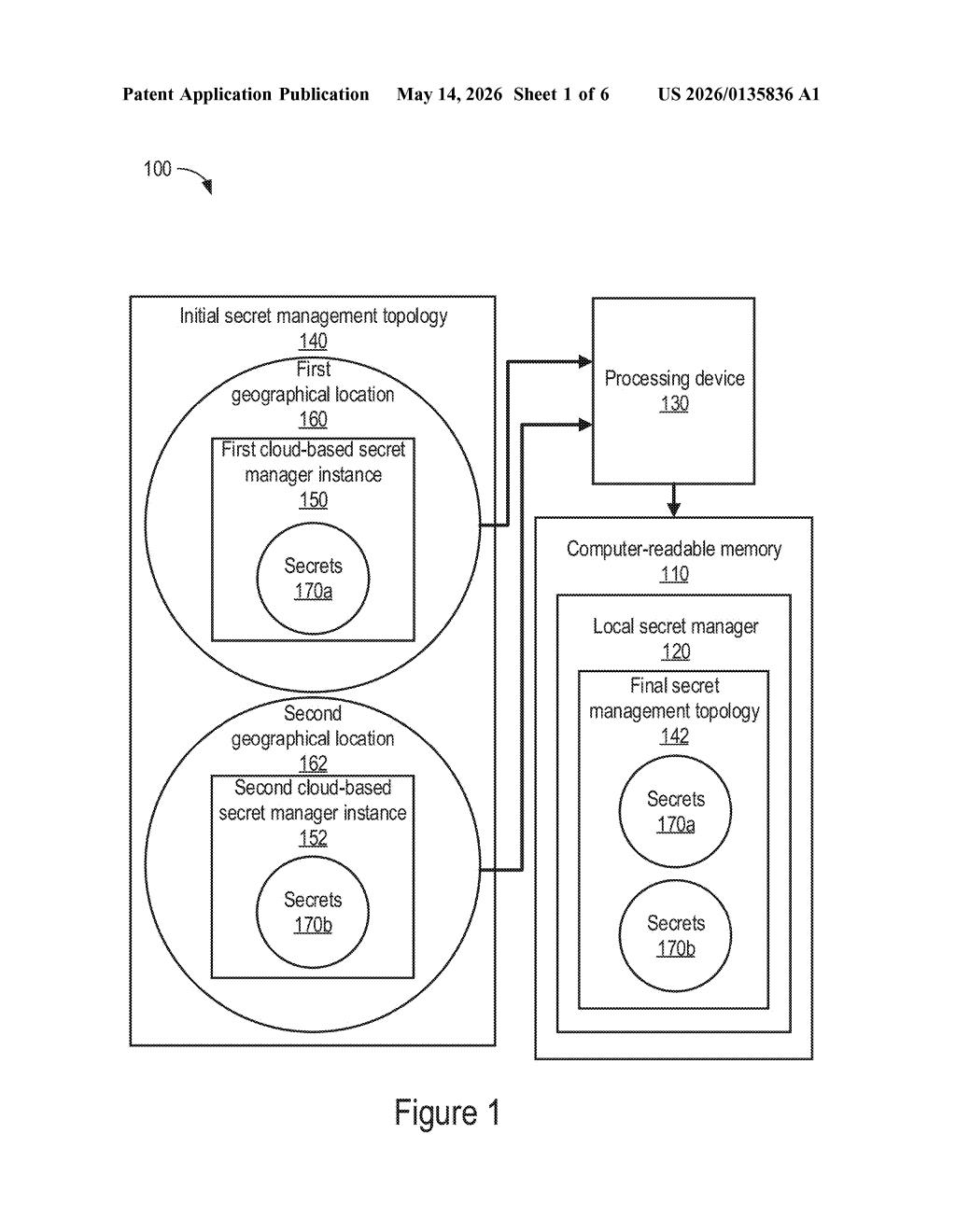
First, a processing device queries one or more cloud-based secret manager instances to extract the initial secret management topology — essentially a map of how secrets are organized. In the described embodiments, the key parameter is geographical location (e.g., secrets belonging to a EU region instance vs. a US-East instance), though the claim language is broader and covers any associating parameters.
Second, each cloud instance is tagged with its respective parameters. This step is what allows the system to avoid the common pitfall of a "flat migration" where all secrets get dumped into a single bucket with no organizational context.
Third, the system migrates the secrets into a local secret manager — an on-premises or self-hosted vault — and organizes them to reproduce the original topology. The result is a final secret management topology that mimics the initial one.
- Reads cloud secret manager structure before migration
- Associates each secret set with location or other parameters
- Writes secrets into local vault preserving that structure
This is a continuation of US Patent 12,556,513 (filed May 2023), so the core concept was already granted — this filing likely broadens or refines the claim scope.
What this means for hybrid cloud security teams
For enterprise security and DevOps teams, moving secrets between secret managers is one of those unglamorous but genuinely risky operations. A botched migration can break CI/CD pipelines, revoke access to production systems, or — worse — leave credentials exposed during the transition window. A tool that automates topology preservation removes a significant manual error surface.
This patent is also timely given the ongoing push toward hybrid cloud and on-premises sovereignty — especially in regulated industries like finance and healthcare in the EU, where data residency rules matter. Red Hat, as a key player in enterprise Linux and OpenShift, has a natural customer base that wrestles with exactly this problem.
This isn't a flashy AI or hardware patent, but it's the kind of solid infrastructure tooling that actually ships and actually gets used. Red Hat's enterprise customer base deals with secrets sprawl constantly, and a topology-aware migration tool fills a real gap. The continuation status means the core patent already passed muster — this filing is about extending the coverage.
Get one Big Tech patent every Sunday
Plain English, intelligent commentary, no hype. Free.
Editorial commentary on a publicly published patent application. Not legal advice.
