Microsoft Patents a Dynamic Compliance-Checking System for App Data Access
Before an app can touch sensitive data, Microsoft's new patent wants to check whether that app is actually playing by the rules — and revoke access the moment it stops.
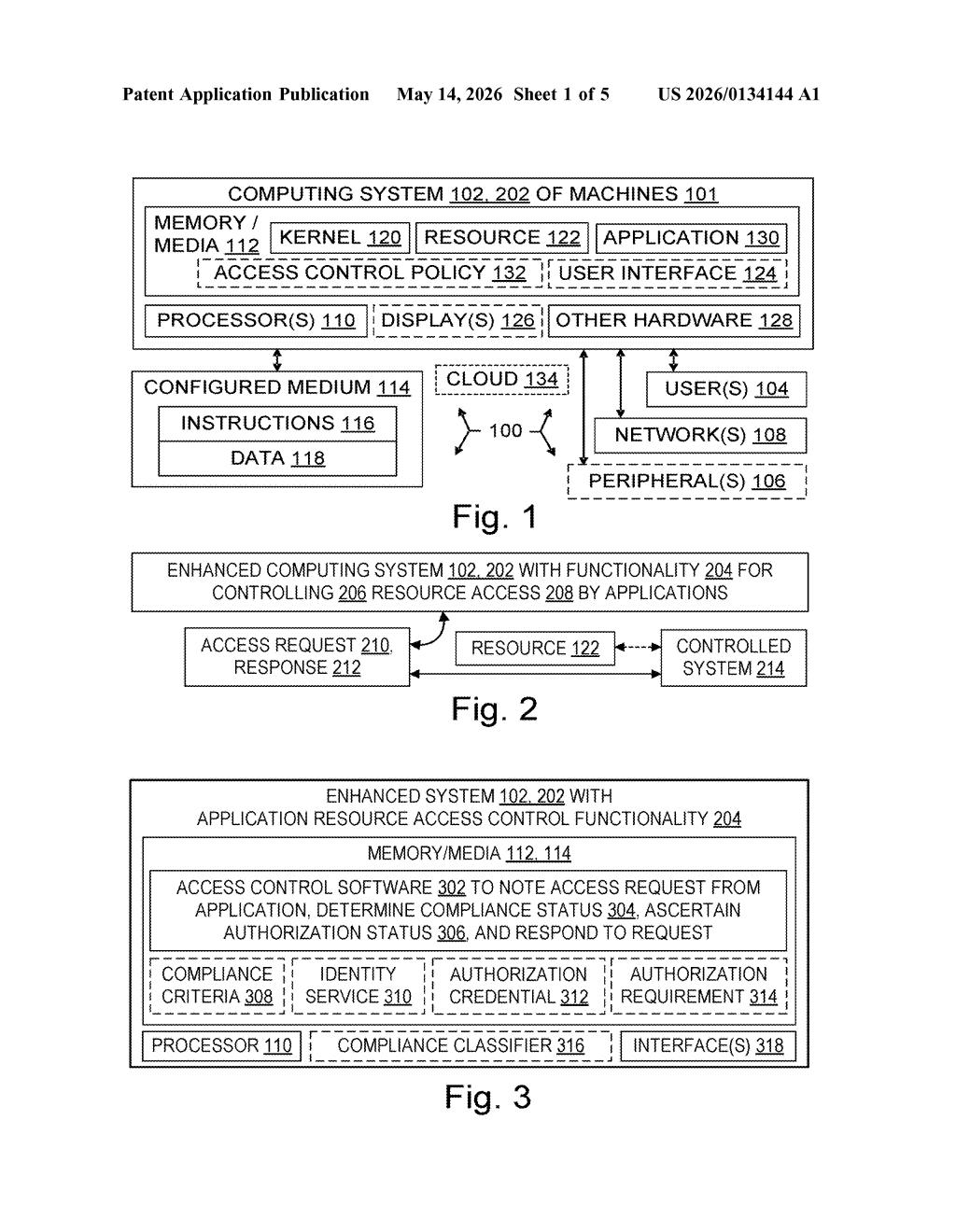
How Microsoft's compliance gate controls app data access
Imagine your company's HR software suddenly fails a security audit — maybe it's running an outdated version or a new policy just kicked in. Normally, you'd have to manually revoke its database access or wait for an admin to notice. Microsoft's patent describes a system that handles that automatically.
The idea is to give every application a kind of compliance score stored in a central identity directory. When the app asks to access something sensitive — say, a file labeled "confidential" — the system checks two things: does the app have the right credentials, and is it still in good standing with your security policies? Both boxes have to be checked.
What makes this interesting is the live monitoring piece. If something about the app changes — a new version rolls out, a policy shifts — the system recomputes its compliance status on the fly and updates the directory. No waiting for a nightly batch job.
How the compliance classifier and identity store work together
The patent describes a two-factor access control system where authorization credentials (the traditional "does this app have permission?") are combined with a new layer: compliance status ("does this app currently meet our security policies?").
Here's the flow:
- A compliance classifier evaluates each application against a set of configurable criteria — things like patch level, configuration state, or policy adherence.
- The result is stored as a compliance attribute inside an identity service (think Azure Active Directory / Entra ID — a central directory that manages who and what has access to what).
- When an app sends an access request, the system queries that stored compliance attribute alongside the app's authorization credential before deciding to allow, deny, or escalate the request.
The clever part is the change event monitor. The system watches application properties that feed into compliance criteria. The moment a relevant property changes — a config file is modified, a new policy is published — the classifier recomputes the compliance status and writes the updated attribute back to the identity store. Access decisions from that point reflect the new reality without any manual intervention.
The patent also mentions grouping apps by resource sensitivity labels, so more sensitive data can be gated by stricter compliance thresholds.
What this means for enterprise zero-trust security
Enterprise IT teams spend enormous effort manually auditing which apps should still have access to which resources, especially after policy changes or software updates. This patent essentially proposes automating that entire feedback loop inside the identity layer — the same infrastructure that already controls logins and permissions in most large organizations.
For zero-trust security (the model where nothing is trusted by default, even inside your own network), continuous compliance verification is the missing piece most implementations struggle with. If Microsoft bakes this into Entra ID or a future version of Microsoft Defender for Cloud Apps, your IT team could get real-time access revocation without writing custom scripts or waiting on quarterly reviews.
This is solid, unsexy enterprise security infrastructure — the kind of thing that quietly ships inside Entra ID or Defender for Cloud Apps and saves IT admins real hours. It's not a flashy AI patent, but automating compliance-driven access revocation is a genuine pain point in large organizations, and Microsoft is clearly building toward a more dynamic zero-trust architecture. Worth tracking if you follow enterprise identity and access management.
Get one Big Tech patent every Sunday
Plain English, intelligent commentary, no hype. Free.
Editorial commentary on a publicly published patent application. Not legal advice.
