Samsung Patents a Chip-Tied Authentication Key System for Secure Storage
Samsung is patenting a way to generate authentication keys that are cryptographically bound to a specific chip's unique identifier — meaning a key cloned from one device simply won't work on another.
How Samsung locks an auth key to your device's chip ID
Imagine someone manages to copy the security credentials off your phone and paste them onto a different device. Without extra protections, that clone could impersonate your phone completely. Samsung's patent describes a way to make that attack much harder.
The idea is to generate an authentication key using the unique ID burned into your phone's main processor chip, then store that key inside a dedicated security module — a separate, hardened chip that handles sensitive operations. Because the key is derived from that specific chip's identifier, a copied key tied to a different chip simply won't match.
There's also a sensible once-only rule baked in: if a key already exists inside the security module, a new one won't overwrite it. That prevents an attacker from quietly replacing a legitimate key with one they control.
How the main IC identifier seeds the key generation process
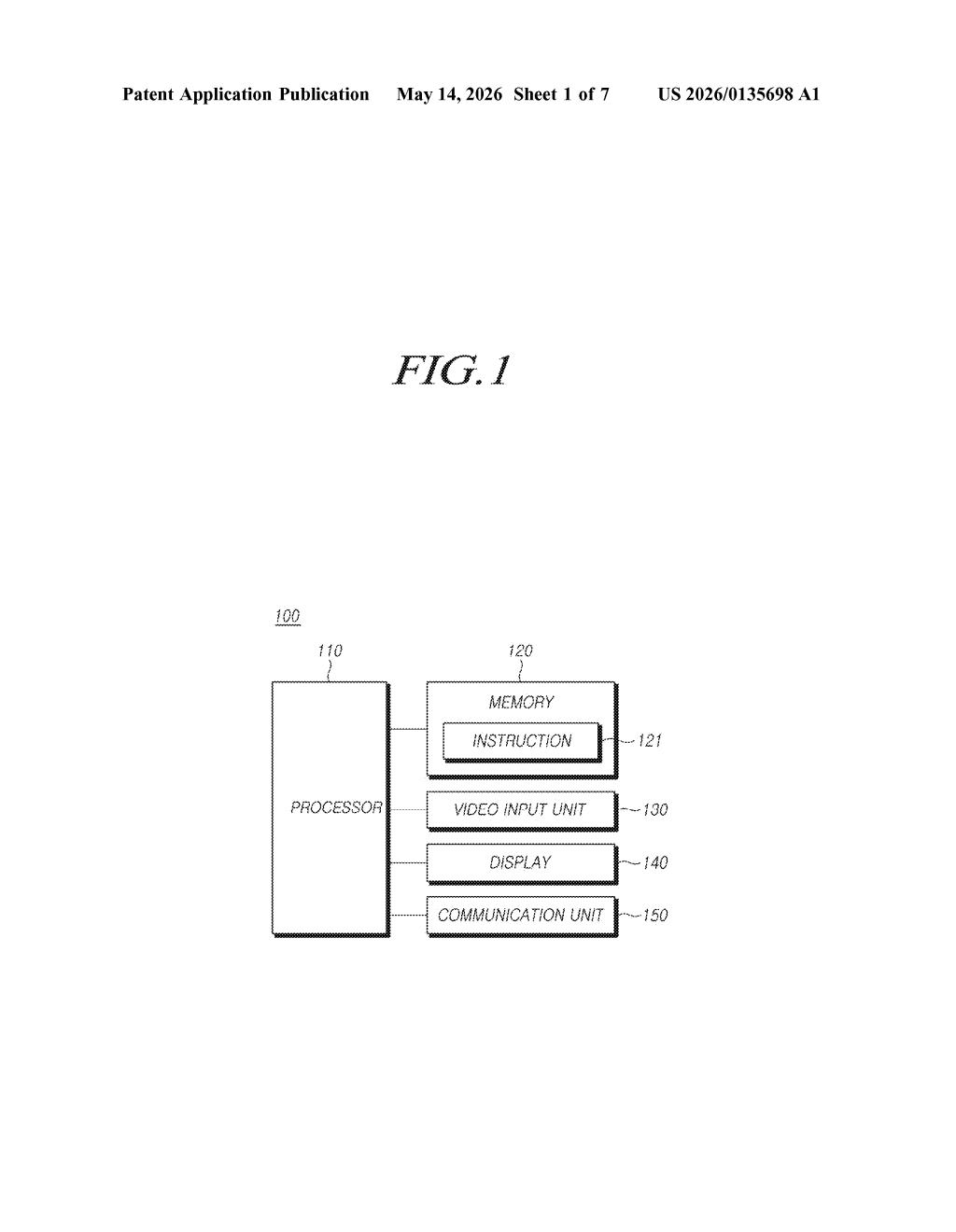
The patent describes a two-component architecture on the device: a general-purpose processor sitting on the main integrated circuit (IC), and a separate security module — think of it like a mini-vault chip that stores secrets and runs security operations in isolation.
When the processor detects a request to store an authentication key, it doesn't just forward a pre-made key. Instead it generates the key on the fly by feeding two inputs into a first security algorithm (a cryptographic function — the patent doesn't pin down which one): the unique identifier of the main IC (a hardware serial number baked into the chip at manufacture) and presumably some additional secret material implied by the algorithm.
That freshly generated key is then transmitted to the security module. The module applies one critical gate before storing it:
- If no authentication key is already stored, the module accepts and saves the new key.
- If a key already exists, the module rejects the new one — preventing silent key replacement attacks.
The result is a key that is both hardware-rooted (bound to a chip ID that can't be software-spoofed) and write-once from the security module's perspective, which limits a whole class of credential-substitution attacks.
What chip-bound keys mean for Samsung device security
Binding cryptographic credentials to a chip's hardware identity is a well-established principle — it's the same logic behind Apple's Secure Enclave and Android's StrongBox. What Samsung is specifically patenting here is the generation flow: the processor derives the key using the main IC's identifier rather than receiving a key from an outside source. That means the key never needs to travel across a network to be provisioned, reducing exposure windows.
For Galaxy devices and Samsung's broader IoT ecosystem, this kind of write-once, hardware-derived key architecture could strengthen protections for payments, secure boot, and device attestation — scenarios where proving "this is the original, unmodified hardware" is critical. It's also the sort of foundational patent that quietly underpins bigger security features you'd actually see marketed.
This is solid, unglamorous security infrastructure work. Hardware-rooted key derivation isn't a new idea in the industry, but Samsung staking a specific claim on the generation-then-store flow with an IC identifier seed is a meaningful implementation detail worth watching — especially as Samsung pushes Knox and its IoT security story harder. Don't expect a press release about this one, but it's the kind of patent that ends up in product specs three years from now.
Get one Big Tech patent every Sunday
Plain English, intelligent commentary, no hype. Free.
Editorial commentary on a publicly published patent application. Not legal advice.
