Qualcomm Patents a Chip That Tightens Its Own Security When It Overheats
Hackers don't just attack software — they attack physics. By deliberately overheating a chip, they can cause it to make computational errors that leak secrets. Qualcomm's new patent describes a system that watches a device's temperature and automatically tightens security the moment things start getting suspiciously warm.
How Qualcomm links chip temperature to hack defense
Imagine someone physically tampering with your phone or modem by blasting it with heat — not to fry it, but to confuse it just enough to bypass security checks. This class of attack, called a thermal fault injection attack, is a real technique used by hardware hackers to extract cryptographic keys or bypass secure boot processes.
Qualcomm's patent describes a chip that monitors its own temperature in real time. When it detects temperatures in certain ranges — ranges that suggest something unusual is happening — it automatically upgrades its own security posture. That might mean switching on additional encryption, adding integrity checks to video data line by line, or temporarily locking down certain functions entirely.
Think of it like a smart thermostat for security: the hotter things get, the more defensive the device becomes. Rather than waiting for an attack to succeed and then responding, the chip acts before damage can be done.
How temperature ranges trigger Qualcomm's security levels
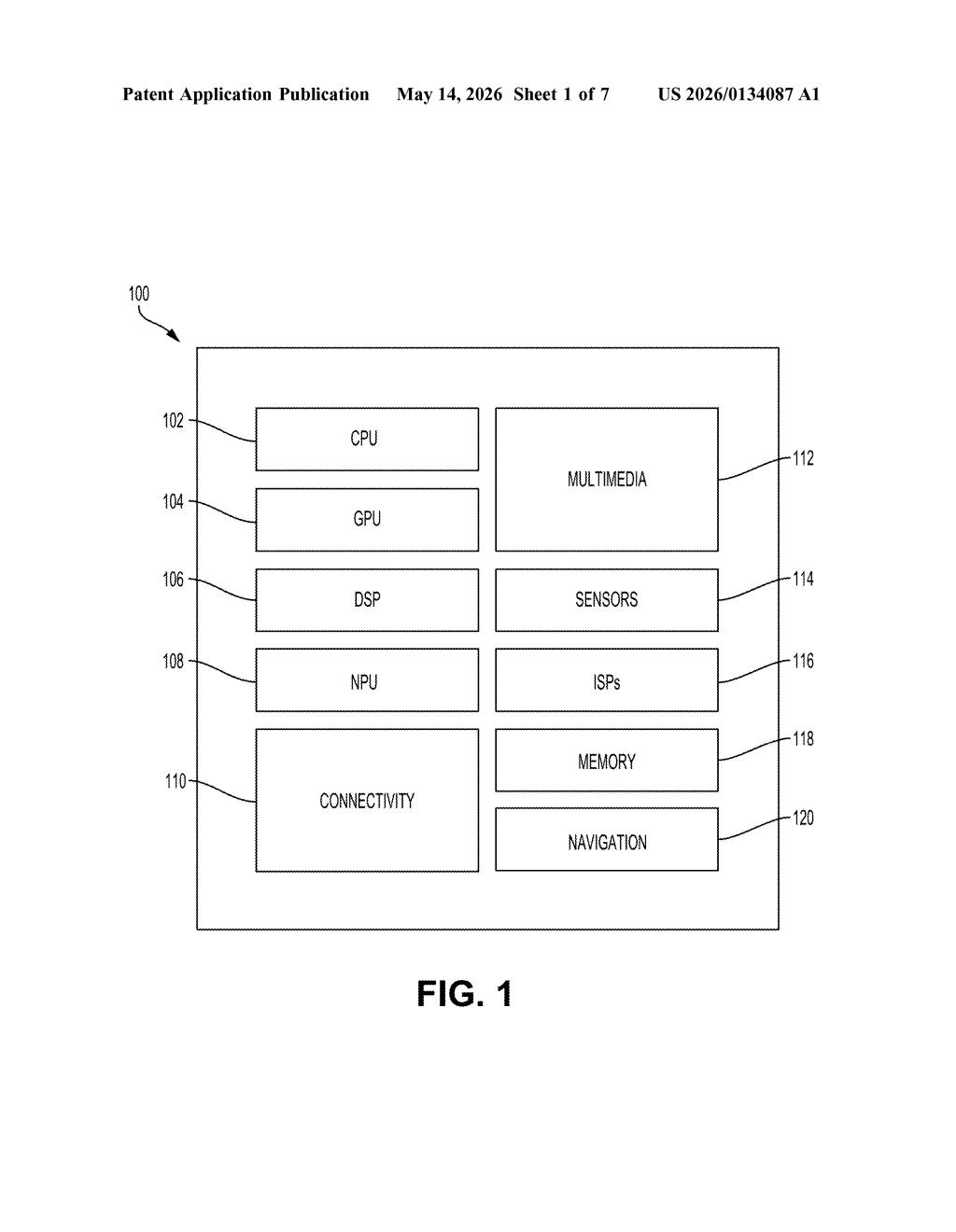
The patent describes an apparatus — likely a system-on-chip (SoC) of the kind Qualcomm puts in phones, modems, and automotive hardware — that continuously monitors its own operating temperature. That temperature reading is compared against a set of predefined temperature ranges, each mapped to a corresponding security level.
As temperatures climb into ranges associated with potential fault injection (where an attacker uses heat to induce computational errors), the device automatically escalates its security posture. The patent's figures show a tiered system with multiple security levels — from no integrity checking at normal temps, up through partial integrity and full integrity modes, with independent controls over encryption (on/off) at each tier.
Concretely, the security actions include:
- Toggling encryption on or off for data paths
- Switching between line-based and byte-based integrity verification for video data
- Adjusting which subsystems (labeled SV-1 through SV-5 in the patent) are actively protected
The system can also return to a lower security level if temperatures normalize, suggesting this is designed as a dynamic, real-time feedback loop rather than a one-way lockdown. The mention of video line integrity checking hints at display or camera pipeline protection — a common target in media security contexts.
What this means for mobile chip security against physical attackers
Physical side-channel attacks — including thermal, voltage glitching, and electromagnetic fault injection — are a growing concern for devices that handle sensitive data outside a controlled server room. Phones, automotive ECUs, and IoT modems are all exposed to environments (and adversaries) that servers never face. A chip that can detect and respond to anomalous heat conditions closes a gap that pure software security can never address.
For Qualcomm specifically, this matters across its entire product stack: Snapdragon mobile chips, automotive compute platforms, and cellular modems all handle cryptographic operations that are attractive targets. If this technology ships in silicon, it would give Qualcomm a tangible hardware-level security differentiator — the kind of thing that enterprise and government buyers increasingly ask about when evaluating mobile chipsets.
This is genuinely clever, purpose-built security engineering — not a paper patent. Thermal fault injection is a documented attack vector with published academic research behind it, and tying security posture dynamically to temperature is a practical, implementable countermeasure. The tiered integrity model for video pipelines is an unexpectedly specific detail that suggests real design work went into this, not just a broad defensive filing.
Get one Big Tech patent every Sunday
Plain English, intelligent commentary, no hype. Free.
Editorial commentary on a publicly published patent application. Not legal advice.
