Microsoft Patents a Real-Time Risk-Scoring System for Human and Bot Identities
When an employee — or an automated script — asks for extra permissions, Microsoft's patent wants a risk score calculated on the spot before anyone says yes. The twist: that score gets handed to a human approver along with a flag for any weird behavior detected in real time.
What Microsoft's identity risk-scoring system actually does
Imagine you work at a company and you need temporary admin access to fix a server. You send a request to your IT team. Now imagine that, at the exact same moment, the system notices your account just tried to download an unusual batch of files. Under Microsoft's patented approach, both pieces of information — your access request and the suspicious activity alert — land in front of the approver at the same time.
That approver can then make a more informed call: grant the access, deny it, or grant a reduced version. Once access is approved, the system keeps watching. If your behavior keeps looking off, your access level can be quietly dialed back — or cut entirely — without waiting for a manual review.
This applies not just to human employees but also to non-human identities like bots, service accounts, and automated pipelines — the kind of accounts that are increasingly common in cloud environments and are often the weakest link in a security breach.
How the anomaly detector gates elevated access requests
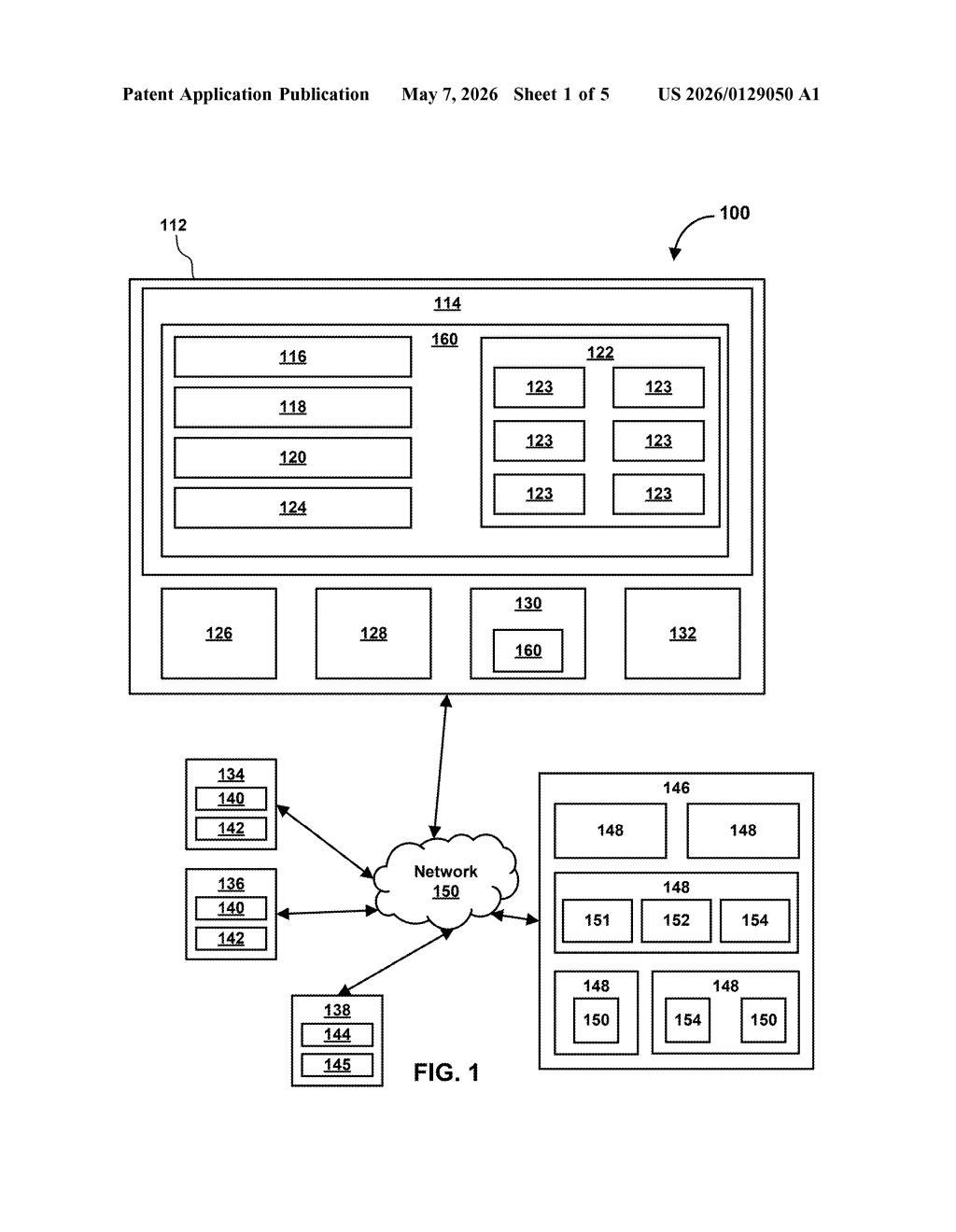
The patent describes a Just-In-Time (JIT) / Just-Enough-Access (JEA) access control system — meaning permissions are granted only when needed and only at the minimum level required, rather than baked in permanently.
Here's the core flow the patent claims:
- A user (human or automated) requests elevated access to a resource.
- The system simultaneously detects anomalous behavior — anything outside the user's normal activity pattern.
- A risk score is assigned to the user based on that behavior.
- The access request and the anomaly notification are bundled together and sent to a second user (an approver) for a decision.
- Depending on the decision, access is granted, adjusted, or revoked — and the system continues monitoring afterward.
The continuous monitoring piece is notable. After access is granted, the system can downgrade permissions dynamically if behavior continues to look suspicious — even before a human manually intervenes. This is sometimes called adaptive access control (access levels that shift in response to live signals rather than being set-and-forget).
The patent explicitly covers both human identities (employees, contractors) and non-human identities (service accounts, APIs, bots) — a distinction that's increasingly important as enterprises run large fleets of automated workloads alongside their human workforce.
What this means for enterprise zero-trust security
Most enterprise access management today is still fairly static: you get a role, you keep it until someone manually revokes it. That gap — between when a threat appears and when access is actually cut — is where a lot of breaches happen. Microsoft's approach closes that window by making the approval workflow itself risk-aware, so approvers aren't flying blind.
For you as an end user inside a large organization, this could mean fewer surprise lockouts (because the system is more surgical) but also faster automatic downgrades if your account shows signs of compromise. For security teams, it's a meaningful step toward zero-trust architecture — the model where no identity, human or machine, is trusted by default, ever.
This is solid, unsexy enterprise security work — exactly the kind of infrastructure Microsoft needs to keep Entra ID (its identity platform) competitive with CrowdStrike and Okta. The non-human identity angle is genuinely timely; service account sprawl is a real and underappreciated attack surface. Don't expect a flashy product announcement, but do expect pieces of this to quietly show up in Microsoft Entra or Defender for Cloud.
Get one Big Tech patent every Sunday
Plain English, intelligent commentary, no hype. Free.
Editorial commentary on a publicly published patent application. Not legal advice. Patentlyze may earn a commission if you click an affiliate link and make a purchase. This doesn't affect what we cover or how we cover it.
