Google Patents a Privacy-Preserving Compute System Blending MPC and Trusted Enclaves
What if you could run a calculation on sensitive data — and none of the computers involved ever saw the raw numbers? Google's latest patent describes exactly that, by chaining together two well-established cryptographic techniques into a single hybrid system.
How Google keeps data secret even while computing on it
Imagine you want to ask a question about private data — say, whether a user qualifies for an offer — without anyone actually reading that user's information. That sounds impossible, but cryptographers have been chipping away at it for decades.
Google's patent describes a system where your input data is split into "secret shares" — meaningless fragments — and sent to separate computers. No single computer ever holds the full picture. Those fragments are then passed into a special isolated environment (called a Trusted Execution Environment, or TEE) that can temporarily reassemble and process the data inside a locked-down hardware vault, then immediately re-scramble the results.
The final answer gets sent back — still fragmented — and only recombined at the end. At no point does any single server, Google-operated or otherwise, see your actual data in the clear. It's a double-layer privacy sandwich: cryptographic splitting on the outside, hardware-enforced secrecy on the inside.
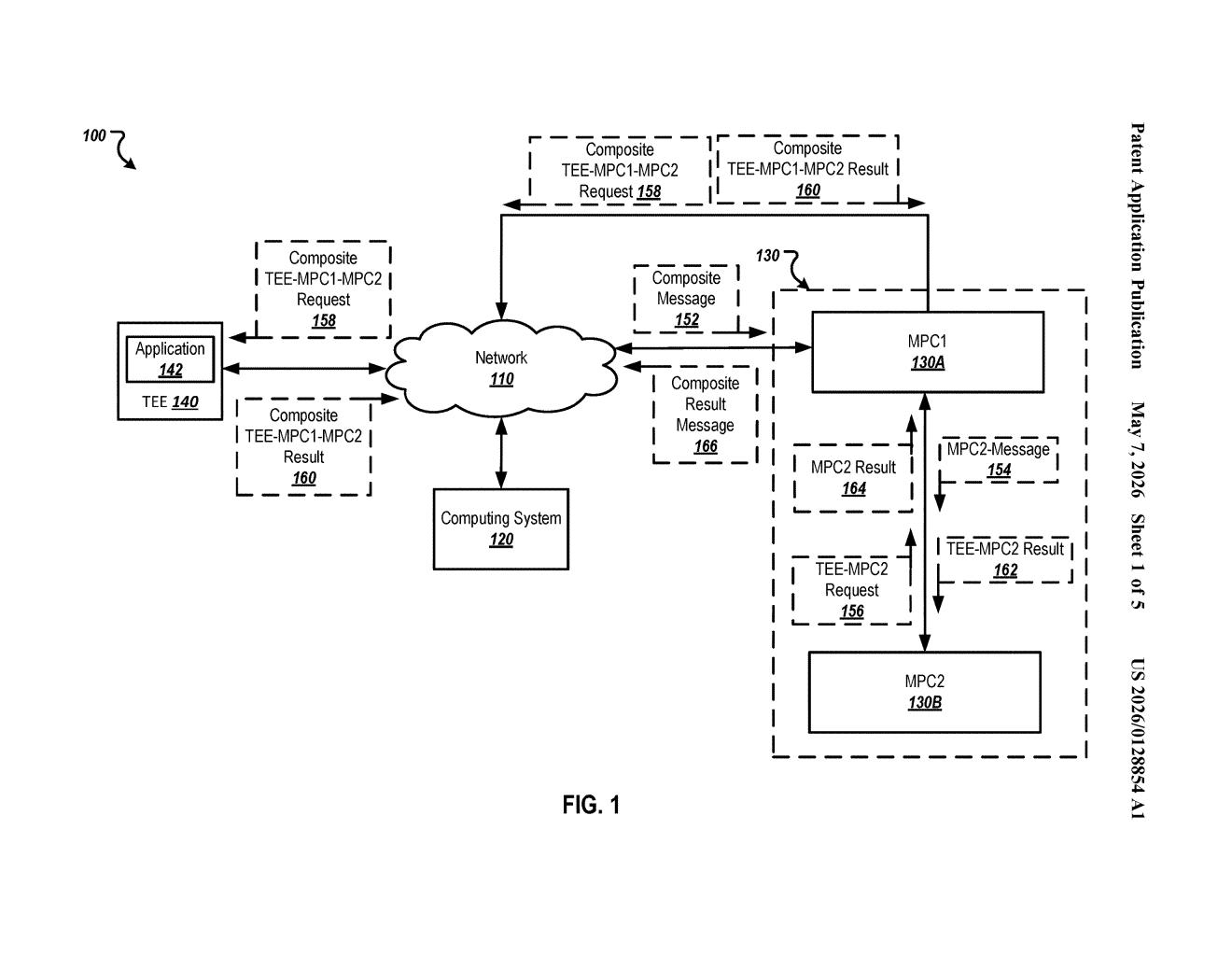
How the TEE-MPC handoff splits and recombines secrets
The patent combines two complementary privacy technologies: Secure Multi-Party Computation (MPC) and Trusted Execution Environments (TEE).
MPC (think of it as splitting a secret into puzzle pieces distributed across multiple servers) ensures that no single server can reconstruct the input on its own. A TEE (a hardware-isolated enclave, like Intel SGX or ARM TrustZone) is a locked room inside a processor where code runs shielded from the rest of the machine — even the OS can't peek inside.
Here's the flow the patent describes:
- A client sends secret shares of its input data to a cluster of MPC systems — each server gets only a fragment.
- The MPC servers forward their respective shares to an application running inside a TEE that sits outside the cluster.
- The TEE reconstructs the plaintext only inside its secure enclave, runs the required computation, then re-splits the output into new secret shares.
- Those output shares go back to the MPC cluster, which performs final secure computations and returns a result share to the requesting system.
The key insight is that MPC alone struggles with complex computations (it's slow and limited), while TEEs alone require trusting the hardware vendor. Combining them means neither weakness dominates — MPC keeps the TEE honest, and the TEE accelerates the computation MPC can't do efficiently.
What this means for private ads, health data, and cloud trust
For Google, which operates enormous ad and data infrastructure, this kind of architecture is directly relevant to privacy-preserving advertising measurement — the kind of computation needed when you want to know "did this ad lead to a purchase?" without any party learning who the user was. It's also applicable to healthcare data joins, financial risk scoring, and any scenario where multiple organizations need to collaborate on sensitive data without trusting each other.
For you as a user, the practical promise is that your data could be part of a computation without ever being exposed in readable form to the cloud servers running it. That's a meaningful shift from today's norm, where "privacy" usually just means a promise in a terms-of-service document.
This is serious cryptographic infrastructure work, not a flashy consumer feature. The combination of MPC and TEEs is a well-known research direction — Google isn't inventing it here — but patenting a specific, production-oriented architecture for how the two systems hand off secret shares to each other is meaningful engineering. Given Google's ongoing regulatory pressure around ad data and its investments in Privacy Sandbox, this feels like foundational plumbing for real systems, not a defensive filing.
Get one Big Tech patent every Sunday
Plain English, intelligent commentary, no hype. Free.
Editorial commentary on a publicly published patent application. Not legal advice. Patentlyze may earn a commission if you click an affiliate link and make a purchase. This doesn't affect what we cover or how we cover it.
